- 01 Apr, 2022
- Topic of the Month

1. Introduction & Definition
‘I don’t need a hard disk in my computer if I can get to the server faster … carrying around these non-connected computers is byzantine by comparison.’ - Steve Jobs, late chairman of Apple (1997)
By reading the above line of reasoning, we can realise how much the relationship between man and machine has changed over the last few decades. Thinking in ‘local’ switched into thinking in ‘local network’ then ‘remote network’ and most recently into the ‘cloud.’ I dare not even think about what will be the next step in the line…
But what do we mean by ‘cloud’ and ‘cloud computing’ in the world of information technology? In our interconnected world, by reaching the nearest server for the key phrase ‘What is the cloud?’ the answer is as follows: ‘The cloud is an idea linked to the concept of distributed computing – a system whereby the hardware, software, and processes making up an IT system may be situated at different locations across the globe, so long as they remain in contact with each other via some sort of communications network.’
So, in its current form, the cloud itself is simply a collection of servers and IT resources owned by some of the world’s largest corporations. Basically, the cloud is simply a ‘floating hardware,’ a lot of metal and steel with nearly infinite computing power.
To exploit and manage this enormous capacity, we use ‘cloud computing,’ which is the on-demand delivery of computing power, database capabilities, storage, and applications over the internet.
More and more applications are cloud-based, and their data are no longer stored on your devices or internal network. A cloud is a place where you can store data and access apps and services easily and quickly. A device with an internet connection is the only thing you need to use your cloud-based programs anywhere and at any time. ‘Cloud storage’ ensures that your data is stored separately from your place of business and can be accessed by any device at any time.
Cloud security refers to the technologies, policies, controls, and services that protect cloud data, applications, and infrastructure from threats. Basically, cloud security is the usage of the latest technologies and security techniques to protect your data, applications and infrastructure associated with cloud computing.
The question immediately arises: why should I trust any cloud providers if I do not even know where my data is? Is it about 5 km from me, or maybe in a server farm somewhere in the North Pole?
Well, you deserve to know how the cloud provider stores and protects your data. You should also have the possibility to make or get recurrent backups of your data in a format that you can easily use in case of disruption of the service. Ideally, you should check that the backups are available and reliable in case of need.
The biggest dilemma in discussing this topic is where we feel more secure our data: on our machine or ‘somewhere’ in the cloud.
This article attempts to answer what threats may affect our data in the cloud, which the most common threats are, and what trends can be expected in 2021.
2. The history of cloud computing
‘In 2000, when my partner Ben Horowitz was the CEO of the first cloud computing company, Loudcloud, the cost of a customer running a basic internet application was approximately $150,000 a month.’ - Marc Andreessen, co-founder of Netscape, Board Member of Facebook.
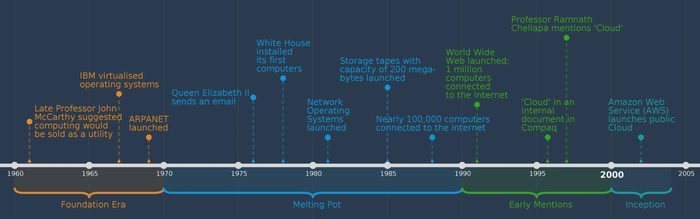
Based on the quote above, there were some people who, even in 2008, did not predict a bright future for cloud-based solutions. But by that time, we have already passed some significant milestones in the development of cloud computing. The figure below shows concisely and clearly the most extensive technological steps that surrounded the growth of cloud computing.
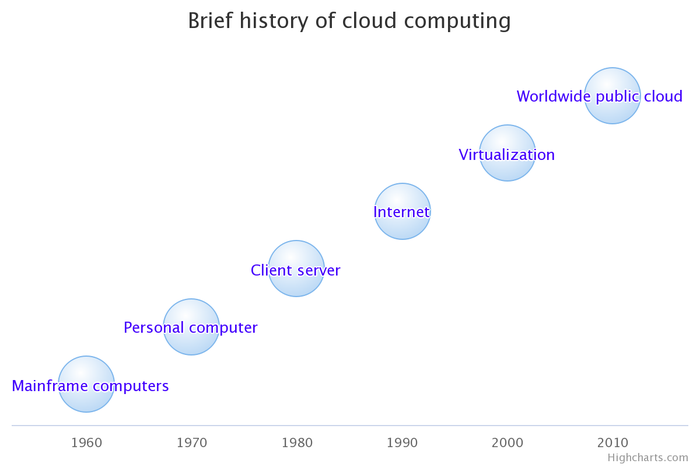
If we look at the development of cloud computing technology in a little more detail, we can distinguish two major stages as follows:
The beginnings
Cloud computing history can trace back to the 1950s. In 1955, John McCarthy, who originally coined the term ‘artificial intelligence’ (AI), developed the theory of sharing computing time. In the 1950s, mainframe computers were large and very expensive: with ‘time-sharing,’ smaller companies with limited financial resources could ‘rent’ some computing time and power.
J.C.R. Licklider was the first director of ARPA (the Advanced Research Projects Agency) who developed further John McCarthy’s theory and came up with the idea for an interconnected system of computers.
The next significant milestone in cloud computing history occurred in 1969 when Bob Taylor and Larry Roberts developed ARPANET (Advanced Research Projects Agency Network). This was the first network that allowed digital resources to be shared among computers that were not in the same physical location.
In 1972, IBM laid the foundation stone of the technology on which the current cloud is built by releasing its operating system called the VM (Virtual Machine).
In 1999, Salesforce introduced the concept of delivering enterprise applications via a website. This made it possible for companies to start delivering apps over the internet in the subsequent years contributed to the birth of the Software as a Service (SaaS) cloud computing model.
The cloud timeline from 2006
In 2006, Amazon Web Services (AWS) launched Elastic Compute Cloud (EC2). This was a significant step in the spread of cloud computing because it enabled private people to rent virtual machines and use them for their purposes online. During this time, the technology was further developed, and solutions focused on empowering data centres making applications more reliable and stable for public users.
The name ‘cloud’ was first used by Eric Schmidt, CEO of Google, at the 2007 Google Conference in San Jose. In the same year, they launched their Google Docs application, which later became a defining milestone in the deployment of office applications in the cloud.
After 2008, datacenters became more widespread geographically.
In 2009, Google started to offer browser-based enterprise applications through services such as Google Apps.
In 2010, Microsoft entered the marketplace and launched Azure services. The OpenStack application was also launched in that year which became very popular among the IT community. By this time, the usage of cloud technologies started to become very popular since it made data sharing easy and became much more accessible financially.
From 2012, it became possible to monitor the resources used on the cloud, so the concept of the cloud became more trusted.
In 2013, Docker introduced open-source container software.
In 2014, AWS Lambda was launched for serverless applications, whereas in the following year, Blockchain-as-a-service was introduced. In the same year, Google released Kubernetes. By 2014, cloud computing had developed its basic features, and security became the primary focus: as cloud security became more and more valuable to customers, cloud security solutions started to proliferate.
In 2016, Cloud-based IoT platforms became available.
In 2017, Amazon launched its Kubernetes-based service, Amazon Elastic Kubernetes Service (EKS). Microsoft released its version, Azure Kubernetes Service (AKS).
The use of cloud computing has also undergone significant changes: what started as simple hosting services has progressed to Infrastructure as a Service (IaaS), Software as a Service (SaaS), Platform as a Service (PaaS), and other solutions. And by today, large-scale cloud computing has been democratised. Although cloud service is concentrated in a few giants’ hands, anyone can access the cloud as a user or tenant.
3. Cloud types and service models - Updated
‘Even if someone builds the Cadillac of cloud services, they’ll be out of business within a year’ - Mark Minasi, Windows Expert, 2008.
3.1. Cloud types
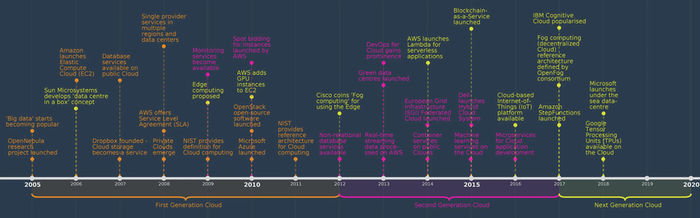
There are five different cloud deployment types:
- Public cloud
- Private cloud
- Hybrid cloud
- Community Cloud
- Multicloud
Public cloud: The services (storage and software) are located off-site, so you need internet to access these services. The most well-known public cloud examples include Google, Amazon, and Microsoft.
Private cloud: In this case, you store data and maintain the software in your infrastructure or by a third party. This solution provides high data security and more control over data.
Hybrid cloud: This solution combines the advantages of both private and public cloud. You may decide which data should be stored in a public cloud and which data should be saved in a private cloud.
Community Cloud: A collaborative, multi-tenant platform used by different organisations. Its users typically operate within the same industry or field and share similar interests or concerns.
To support complex business processes, most companies need a complex IT solution portfolio. As the cloud becomes an increasingly accepted service model for IT solutions, more and more companies are using unique IT features from different vendors’ cloud environments. One of the most obvious solutions to this problem may be the usage of a multicloud model.
Multicloud: it is the use of multiple cloud computing and storage services in a single heterogeneous architecture. It means that a company uses more than one cloud service from more than one provider. For example, a company might use its mail system from a public cloud (in the Software as a Service model). In contrast, the same company uses another public cloud-based Software as a Service solution to perform customer relationship and enterprise management functions. In contrast, a private cloud-based solution is used for database-related purposes (for backing up in an Infrastructure as a Service environment).
In practice, there can be several reasons why companies implement such a solution. They may simply do not want to rely on a single supplier, or they want to operate more cost-effectively and flexibly. It can also happen that they can only comply with local regulations that oblige them to store specific data in their country/region.
So ‘multicloud’ refers to the presence of more than one cloud deployment of the same type (public or private), sourced from different vendors. Hybrid cloud, on the other hand, refers to the presence of multiple deployment types (public or private) with some form of integration or orchestration between them.
Hybrid and multicloud are mutually exclusive: you cannot have both of them simultaneously because the clouds will either be interconnected (hybrid cloud) or not (multicloud).
3.2. Service models - Updated
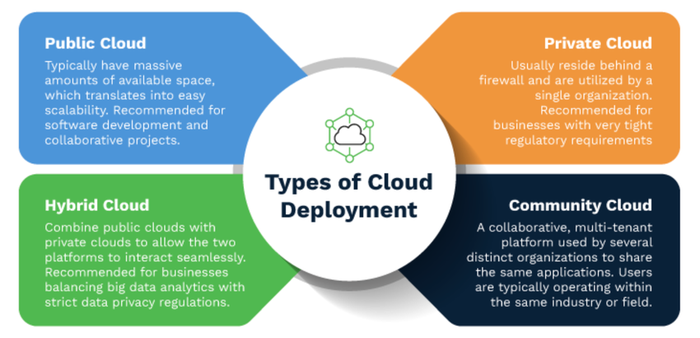
The three main service models of the cloud are one of its strength:
IaaS (Infrastructure as a Service): The cloud provider provides the infrastructure (predefined number of processors, RAM, storage space, etc.), and you must install and manage your own operating systems and applications. You just ‘rent’ computing infrastructure online from a specialised company (cloud provider), and this company is only limited to maintain the hardware components (storage capacity, network, operating system).
You may request more speed, processors, RAM or storage space and so you can react dynamically to peak needs without funding the infrastructure year-round. Another advantage of this model is that you ‘pay as you go’, which means you should only pay for the period the resource has been used.
PaaS (Platform as a Service): on top of the IaaS model, the cloud provider makes the infrastructure available for you and adds the operating system layer and a production environment such as web servers or database servers. In this case, you only need to set up your applications on the infrastructure because the cloud provider manages everything else.
SaaS (Software as a Service) is the most popular among users and businesses. In this model, users use any browser to access the service, rather than a particular application in the case of the IaaS or PaaS model. The cloud provider supplies the needed application as well. You do not need to manage anything and can focus on just using the application provided.
According to the forecasts of Statista, the global public cloud services market is expected to grow by about 22 per cent in 2022. That means cloud services will be worth about $ 482 billion.
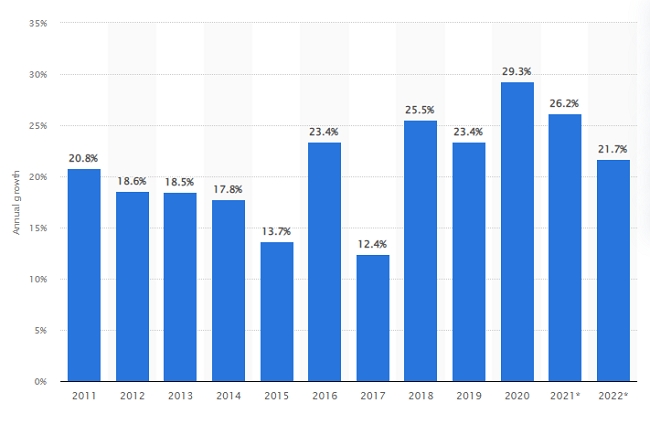
Market growth forecast for public cloud services worldwide from 2011 to 2022 (forecasted) - Statista
3.3 Content Distribution Network (CDN)
It is a general trend that internet users are becoming more and more impatient even with a download delay of one or two seconds, they tend to navigate away from a particular website.
Well, the trend is not new: in the late 1990s, when the internet began to become a mission-critical medium for people and businesses, CDNs were put into service for alleviating internet performance bottlenecks.
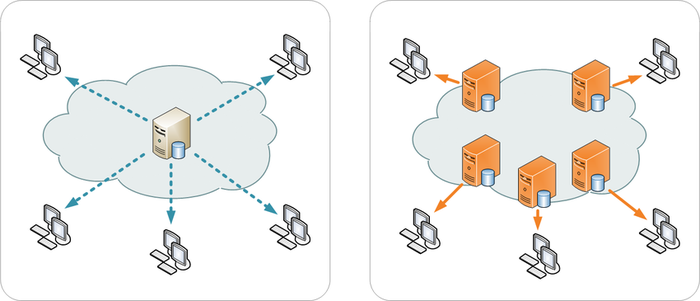
A Content Delivery Network or Content Distribution Network (CDN) refers to a geographically distributed group of servers that work together to provide fast delivery of internet content. A CDN itself does not host content, but it caches it, which improves website performance. The goal of a CDN is to provide high availability and performance by distributing the service in space relative to end-users.
The benefits of using a CDN are as follows:
- Improve website load times
By using a CDN server, visitors experience faster page load times because they download content from a geographically closer server and thus receive the requested information faster.
- Reduce bandwidth costs
Using a CDN reduces unnecessary data traffic and thus reduces site owners’ hosting costs.
- Increase content availability and redundancy
Thanks to their distributed nature, a CDN can handle more traffic and provide redundancy.
- Improve website security
A CDN may improve security by providing DDoS mitigation, improvements to security certificates, and other optimisations. Information security is an integral part of a CDN.
Single server distribution (left), Content Delivery Network (right):
4. Advantages and disadvantages of cloud computing
‘It takes 20 years to build a reputation and few minutes of cyber-incident to ruin it.’ - Stéphane Nappo, Global Chief Information Security Officer at Société Générale International Banking
Maybe we do not like cloud computing, but we need it. What’s more, we have to admit that not only do we need it, but we are reliant on it, and we cannot even exist without it. An inconceivable amount of data for the human brain must be stored, managed, and protected at all times. This is no longer possible with the good old ‘save it to a floppy disk’ method. To support this, let me share with you some statistics from the site of TechJury:
- 463 exabytes of data will be generated each day by people as of 2025 (Raconteur)
- 2.5 quintillion bytes of data are produced by humans every day (Domo)
- Skype has 3 billion minutes of calls per day (Earthweb)
- There are 4.66 billion active internet users around the world (FinancesOnline)
- 59.5% of people around the world have access to the internet (FinancesOnline)
- 333.2 billion emails are sent per day (Earthweb)
- People spend $1 million per minute online (Earthweb)
4.1. Advantages
Cloud computing is a popular option for people and businesses for several reasons, including cost savings, increased productivity, speed and efficiency, performance, and security. The benefits of rapid and easy deployment, low upfront costs, flexibility and scalability have made cloud computing virtually universally adopted. Let’s see the advantages a bit closer:
Maybe this is the only solution
At this moment, this seems to be the only viable solution for storing and protecting the vast amount of data mentioned above.
Low upfront costs
Storing your data in the cloud instead of doing so on your servers saves investment. You do not need to purchase servers, racks, build and operate server rooms. This leads to lower costs due to reduced overhead, less hassle in maintaining and upgrading your servers.
Rapid deployment and scalability
Renting space on the net can be very flexible and allows you to react quickly to increase or decrease the space required, depending on the moment’s needs. Therefore, the cloud is a real opportunity for start-ups who want to develop quickly without making large IT investments.
Omnipresence
Using the cloud makes it possible to work almost everywhere, regardless of where you are what device you use.
Security
The cloud can be an advantage in terms of security. Cloud service providers take essential steps to secure data, and it can generally be considered that data security is higher on the cloud than on a local server. Giant cloud providers like Microsoft, Google or Amazon have gathered a lot of security and compliance experience and dedicate huge teams of people to security only. Traditional IT solution providers cannot compete with them and reach the same level of security.
Availability
Depending on the classification of the data that will be stored in the cloud, availability and connectivity will be criteria to keep in mind. The availability is typically expressed as a percentage: availability of 99.99% indicates that the service might be unavailable for less than an hour a year, without any compensation you are due. If the availability is only 99%, the cumulative downtime could exceed three days.
Connectivity
Availability can be reduced by poor connectivity. The connectivity is determined by the rate offered by your service provider and the cloud provider. The smallest value defines the bottleneck. It is, therefore, necessary to verify that the announced speeds are real and sufficient for the use that will be made of the cloud.
Proper logistics of computing power
Cloud computing removes the limitations of low memory storage, graphical capability, and processing power. Cloud computing for big data analytics allows for the storing and processing of significant amounts of data, which remains readily available, scalable, and fault-tolerant through hardware virtualisation. Cloud platforms can dynamically expand to provide storage for increasing volumes of data.
Big data analysis automation
Cloud computing also provides options for automating the various components of the analytics process, thereby reducing complexity and enhancing big data analysis productivity.
Cloud compliance
It ensures that cloud service providers meet compliance requirements. Data transfer, storage, backup, retrieval, and access necessitates cloud compliance. There are industry and location-specific regulations like PCI DSS (for credit card payments), HIPAA (for healthcare), GDPR (location specific for the EU) and many more. There are also security-centric frameworks like ISO 27001, NIST Cybersecurity Framework, CIS Controls, and CSA STAR, to mention some.
4.2. Disadvantages
Risk of data confidentiality
Like it or not, you are not alone in the cloud, and your data is stored together somewhere with an unknown number of other people. You are a tenant, and as such, you have to share resources. And yes, there is always a risk that your data can be accessed by other people.
The whole system depends on an internet connection
The cloud can only be reached over the internet. Simply put, no internet, no cloud. It may sound strange not to have internet (are not we too dependent on it?), yet it often happens that there is no connection somewhere for some reason. Remember that many things have to work well at once to have a good internet connection without any problems…
Independence
The relationship with an IT service provider always entails a certain dependence. When you use a cloud computing system, you are entirely entrusted with data security and confidentiality to companies that provide cloud computing servers.
Data mobility
This refers to the possibility of sharing data between cloud providers. How can the data be transferred to another provider? What happens in the event of supplier bankruptcy?
Customer support
In case of a problem, you need to contact the helpdesk. You may have concerns about how fast they will react and fix your issue, should you pay any extra?
Security
Probably the most doubtful thing related to cloud computing is security. The problem is that cloud service providers are also a prime target for hackers, given the large amount of data residing there. This way or the other, this boils down to one thing that is always behind our decision and relation to cloud providers: trust.
We do not know personally with whom we do business through a website. We enter into a contract impersonally and anticipate confidence in the service provider that everything will work fine. We should admit that it goes against our principles and our way of thinking. If our data is at hand, it cannot be stolen, but if we do not know where our data is, it is as if it has already been half stolen.
Maybe this industry needs some more time to earn its trust: after all, there are still some people who like to keep their money under the pillow, but most of us keep our money in a bank…
5. Protect and Prevent: Is cloud security wishful thinking or reality? - Updated
‘Cloud computing is often far more secure than traditional computing because companies like Google and Amazon can attract and retain cybersecurity personnel of a higher quality than many governmental agencies.’ - Vivek Kundra, Executive Vice President at Salesforce.com.
Cloud security is the protection of data stored online via cloud computing platforms from theft, leakage, and deletion. It refers broadly to measures undertaken to protect digital assets and data stored online via cloud services providers.
Methods of providing cloud security include data encryption, two-factor authorisation (2FA), firewalls, penetration testing, obfuscation, tokenization, virtual private networks (VPN), and avoiding public internet connections.
Cloud computing is the delivery of different hosted services through the internet, including data storage, servers, databases, networking, and software. Rather than keeping files on a proprietary hard drive or local storage device, cloud-based storage makes it possible to save them to a remote database.
Cloud security is a top priority for cloud storage providers. Besides satisfying their customers, they also need to follow specific regulatory requirements for storing sensitive data such as credit card numbers, passwords, confidential company information, sensitive health information, etc.
5.1. Major threats
Significant threats to cloud security include data breaches, data loss, account hijacking, service traffic hijacking, poor choice of cloud storage providers, insecure application program interfaces (APIs) and shared technology that can compromise cloud security.
Distributed denial of service (DDoS) attacks are another threat to cloud security. These attacks shut down a service by overwhelming it with data so that users cannot access their accounts, such as bank accounts or e-mail accounts.
Another cloud security issue is that data stored on a cloud-hosted in another country may be subject to different regulations and privacy measures.
The Cloud Security Alliance (CSA) recently conducted a survey of industry experts about the most outstanding security issues in cloud computing. As per their survey, these are the top 15 cloud security threats:
5.2. Top cloud security challenges - Updated
1. Data breaches
Breaches can cause great reputational and financial damage and could potentially result in loss of intellectual property and significant legal liabilities. Defining who has access to data is a pivotal question to resolve and protect. Encryption can protect data, but with a trade-off in performance and user experience.
2. Inadequate identity and access management
Inadequately protected credentials, lack of automated rotation of cryptographic keys, passwords and certificates, failure to use multi-factor authentication or strong passwords cause threats. Granular privilege and key management should be implemented to avoid granting extensive privileges beyond what is intended or required. Improperly configured keys and privileges increase the chance of security risks.
3. Insecure interfaces and APIs
Application Programming Interfaces (API) security is of prime importance. Their vulnerabilities can give attackers a clear path to stealing user or employee credentials.
4. System vulnerabilities
Another type of threat is when a company becomes operational in the cloud using security infrastructure and strategies that were not designed for it. The company’s security architecture needs to align with business goals and objectives.
5. Account hijacking
It is a significant threat that can cause a great deal of disruption, including theft or destruction of important data, halting service delivery, or financial fraud.
6. Insider threats
Insiders can be current or former employees and contractors, and they do not need to have malicious intent to cause damage.
7. Advanced persistent threats
Advanced Persistent Threats (APTs) steal data and Intellectual Property (IP) by infiltrating target companies’ IT systems. They are challenging to detect and eliminate (especially spear-phishing attacks) and may only be limited by the introduction of proactive security measures.
8. Malware injection
These are malicious scripts or codes that enable attackers to eavesdrop, steal data and compromise the integrity of sensitive information.
9. Data loss
Another significant cloud-related security risk is data loss. It can have several reasons like a virus or a system failure, and as opposed to information being stolen and distributed in case of data loss, it is erased entirely. Data loss can be damaging for a business: lost data can be difficult or impossible to recover, and the recovery attempts require a lot of time, resources, and financial expenditures.
10. Insufficient due diligence
Organisations migrating to the cloud often perform insufficient due diligence. They move data to the cloud without understanding the security measures used by the cloud service provider and their responsibilities to follow security measures. By failing to do so, they expose themselves to a number of security risks.
11. Poor IP protection
Handing over sensitive data to a third party is always risky. It is no different in the case of intellectual property (IP). Safeguarding critical corporate data demands the highest encryption and security protocols. Do not forget: it can happen that a cloud-based solution might not be a good fit in your situation.
12. Abuse of cloud services
Cybercriminals may use cloud computing to target their victims and use the cloud service against them. Large-scale automated click fraud, DDoS attacks, phishing attempts, hosting of malicious or pirated content in the cloud, e-mail spam, digital currency ‘mining’ are just some examples of misuse of cloud resources.
13. DDoS attacks
A distributed denial-of-service (DDoS) attack is a malicious attempt to disrupt the normal traffic of a targeted server, service or network by overwhelming the target or its surrounding infrastructure with a flood of internet traffic. The majority of DDoS attacks have limited ambition of killing a service entirely but rather significantly impair customer experience. In the majority of cases, DDoS attacks remain unnoticed…
14. Vulnerabilities caused by shared technology
Managing security consistently across different cloud deployment types and service models for geographically distributed organisations often pose a great challenge on cloud providers.
15. Communication with CSPs
It is imperative to understand that cloud service providers (CSPs) use a shared responsibility model for security. It means that CSPs accept responsibility for some aspects of security only. Other aspects of security are shared between the CSP and the consumer, while some security aspects remain the sole responsibility of the customer. Therefore, you should carefully read the Service Level Agreements (SLAs) with CSPs and understand your obligations to comply with cloud security measures.
Adequate cloud security depends on knowing and meeting all consumer responsibilities. Consumers’ failure to understand or meet their responsibilities can easily cause security incidents in cloud-based systems.
Besides the threats detailed above, the following are worth mentioning:
Complex environments
The complexity of cloud-based resources makes them difficult to configure: misconfiguration and inadequate change control are the most common source of errors. One of the best-known examples is the Exactis incident, where the provider left an Elasticsearch database with the data of 340 million US consumers publicly accessible due to misconfiguration. It is not just the loss of data that companies have to face, but the deletion or modification of resources done with the intent to disrupt business. Traditional change management approaches are not effective in the cloud environment.
Increased attack surface
Where there are more fish, there are also more anglers. This is also true for data: where there is more data, there are more cybercriminals. It is not a surprise that the public cloud environment has become a large and highly attractive attack surface for hackers.
Ever-changing workloads
Cloud assets are provisioned and decommissioned dynamically where traditional security tools are incapable of enforcing protection policies successfully.
Cloud compliance and governance
All the leading cloud providers have aligned themselves with the most well-known accreditation programs such as NIST 800-53, HIPAA, PCI 3.2, and GDPR. However, customers are also responsible for ensuring that their data processes are compliant. The compliance audit process is very complex and almost impossible to perform unless tools are used to achieve continuous compliance checks and issue real-time alerts about misconfigurations.
6. Top 10 cloud computing trends for 2022 - Updated
‘94% of the worldwide workloads will be controlled by the leading cloud data centres of the world’ - According to the study of Cisco
To understand what we can expect in 2022, we need to talk about the previous two-year period most of us want to forget. The pandemic hit with elemental force: companies started to close their offices, and working remotely became a new norm. Many employees took their laptops home, and the companies’ IT infrastructure was put to the test never seen before.
Cloud was indeed an area that helped many companies quickly adjust by increasing their computing workloads and licenses. Businesses that had stayed with on-premise solutions struggled to meet the new needs of employees. Solutions that supported remote access and security got priority.
Organisations that enabled remote working discovered the benefits of leveraging cloud solutions. Those who had not used a cloud-based solution before the pandemic found themselves at an insurmountable competitive disadvantage. Amid a pandemic, more and more organisations turned to cloud solutions that can be deployed without the dependencies that traditional on-premise solutions bring.
So if we assume that there is always something good about everything bad, we can say that in addition to the many harmful effects of the pandemic, perhaps the only ‘beneficial’ effect is related to cloud technology. At the outset of the pandemic, most cloud providers could not adequately address the sudden increase in expectations and needs, but this has improved over time.
The 2020-21 period has been an enormous challenge for all industries. First, companies were hit suddenly and unexpectedly by the new situation that arose due to the pandemic and the sudden massive increase in demand for telework. This shift toward cloud platforms and telecommuting has been intensified further in 2022. However, companies are better prepared for this situation, and many already see telecommuting as a full-time model.
Gartner reports that cloud-based adoption grew 23% in 2021 (to a total value of $ 332 billion) and is expected to reach $ 400 billion by 2022.
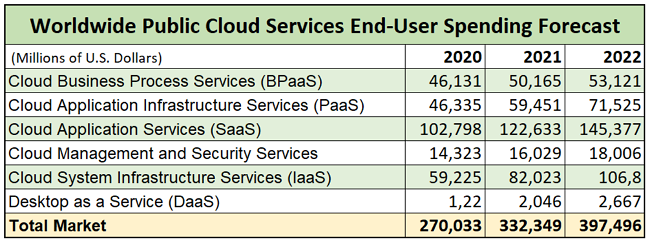
Public cloud services end-user spending forecast - Gartner
Cloud and cloud-based services are essential today, and in this chapter, we look for the answer to what trends we can expect in 2022.
6.1. AI and cloud computing
Artificial intelligence will be one of the most valuable technologies in cloud computing. As technology advances, newer methods are being used to incorporate artificial intelligence into big data processing.
The purpose of using AI solutions is to improve the efficiency of cloud platforms. AI supports organisations in intelligent management and automation of internal processes. By using AI, organisations can adapt to their rapidly changing business needs more effectively. Also, enormous performance and bandwidth from cloud-based data centres are essential to meet the high demands of machine learning platforms.
For further information relating to AI, please consult the article: AI the next wave of digitalisation.
6.2. Boom in cloud gaming
Cloud-based games are expected to become more widespread in the coming years. Platforms like Google Stadia and Amazon Luna will set the direction for the development of cloud-based games in 2022.
The proliferation of online games will positively impact the market value of cloud-based games and the further spread of cloud-based services.
6.3. Hybrid and multi-cloud infrastructure
In 2021 we saw the dominance and spread of hybrid cloud computing. The primary interests in using hybrid cloud solutions were ideal speed, remarkable control, and improved security.
By 2022, the situation has changed. Companies have understood that cloud-based data management does not necessarily mean creating and deploying a single, specific cloud platform or infrastructure but choosing and deploying a platform that suits their situation the most.
6.4. Serverless computing
After the rise of cloud-based platforms, IT companies are switching to a serverless computing model, which promises a cost-effective way of building and operating applications in the cloud. With this trend, we are slowly moving towards a world where developers may not need to rely on physical infrastructure to run codes.
Serverless computing is the abstraction of servers, infrastructure, and operating systems. Serverless computing lets developers shift their focus from the server level to the task level, making them more efficient while the process of ‘code creation’ is cheaper.
The cloud providers call their serverless services Function-as-a-service (FaaS), and users of this technology are only billed for when their code is running.
6.5. The Edge
Edge computing can also be considered a cloud, but the cloud infrastructure is locally distributed in several locations in the case of edge. The most significant advantage of this over-centralised cloud is that it is geographically closer to the user, thus providing more bandwidth and lower latency.
Companies that use cloud-based technologies are more likely to meet their hosting and computing performance needs with edge computing due to the advantages just mentioned. This trend is likely to intensify further in 2022.
6.6. Hyper-scale datacenters
Organisations need an IT infrastructure that can be scaled up rapidly to meet their increased demand. In the business of the digital age, this demand has made the need for large-scale datacenters indispensable. In Luxembourg, the supercomputer called Meluxina is a critical element of the data-driven innovation strategy of the Ministry of the Economy. Pascal Steichen, CEO of SECURITYMADEIN.LU has recently interviewed Prof Pascal Bouvry, CEO of Luxprovide, and they were talking about the Meluxina project as well.
In addition to centralised datacenters and supercomputers, companies are turning to a new solution called SASE (Secure Access Service Edge). This IT security approach allows organisations to quickly take on new cloud services and ensure the protection of their systems.
SASE is a security framework that requires the transformation of security and networking technologies into a single cloud-based platform for secure and fast cloud-based transformation.
6.7. Data security and compliance remain critical
Secure management of exponentially increasing amounts of data will remain essential and even more critical than ever before. As more and more businesses migrate their services to the cloud, regulation compliance and security become an increasing concern. In May 2018, the EU’s General Data Protection Regulation (GDPR) came into effect. However, cloud computing compliance under the GDPR is not easy, and many organisations are still not prepared for it.
6.8. Joined services of big data, cloud computing and IoT
In the future, cloud computing will be more intertwined with big data and IoT for an organisation to improve its production. Leveraging big data capabilities and incorporating machine learning into data interpretation can further increase the thoroughness and efficiency of decision-making.
6.9. Automated cloud orchestration and optimisation
Automated service and performance management will be the most important criteria when choosing a cloud provider in 2021, as organisations may need to deal with a hundred or more services from a single cloud provider.
6.10. Disaster recovery services
As more and more companies store and use an increasing amount of data in the cloud, avoiding downtimes will be increasingly valued, and the cost of downtimes, therefore, will increase dramatically.
- Cloud computing is a popular option for people and businesses for several reasons: cost savings, increased productivity, speed and efficiency, performance, and security. The benefits of rapid and easy deployment, low upfront costs, flexibility and scalability have made cloud computing virtually universally adopted.
- The cloud can be an advantage in terms of security. Cloud service providers take essential steps to secure data, and it can generally be considered that data security is higher on the cloud than on a local server.
- Giant cloud providers like Microsoft, Google or Amazon have gathered a lot of security and compliance experience and dedicate huge teams of people to security only. Traditional IT solution providers cannot compete with them and reach the same level of security.
7. Global players of cloud computing - Updated
‘Every kid coming out of Harvard, every kid coming out of school now thinks he can be the next Mark Zuckerberg, and with these new technologies like cloud computing, he actually has a shot.’ - Marc Andreessen, co-founder of Netscape, Board Member of Facebook.
Many cloud computing companies are battling for a share of the market, particularly as the shift to remote work and videoconferencing are accelerating the adoption of the cloud. This section looks at the most influential cloud-based service providers on Earth who determine the direction and future of cloud computing development.
Amazon Web Services (AWS) was the first major commercial cloud computing service provider offering IaaS services since 2008. Amazon Elastic Compute Cloud (AWS EC2) provides a scalable infrastructure for companies that want to host cloud-based applications.
AWS has the most extensive portfolio with over 170 services, and a 33% share of the cloud infrastructure services market, as per Statista.
Microsoft Azure is the second in the cloud computing market, with an estimated 21% share of the cloud market. Microsoft also formed partnerships with server vendors to target the hybrid cloud markets (Azure Arc, Azure Stack, and Azure Stack Edge).
Google Cloud is the third, with 10% of the market. It is one of the leading cloud computing providers building partnerships with key enterprise players such as Salesforce, Informatica, VMware, and SAP.
Alibaba Cloud is the fourth on the list, with a 6% market share. It is also known as Aliyun, is a Chinese multinational cloud computing company. It provides cloud-computing services to online businesses and Alibaba’s e-commerce ecosystem.
IBM cloud computing is also among the ‘big players’ league with a share of 4%. The company is looking to align its hybrid cloud and AI portfolio to meet the market’s evolving needs. One area of innovation where IBM and others in the cloud computing sector are fostering innovation is developing a quantum computer cloud. Quantum computers use quantum bits (or Qbits), making much faster processing speeds possible. This facilitates the modelling of very complex scenarios and makes it possible to use quantum computers in machine learning and artificial intelligence projects.
Other significant players in the cloud computing market include Salesforce (3%), Tencent (3%) and Oracle (2%).
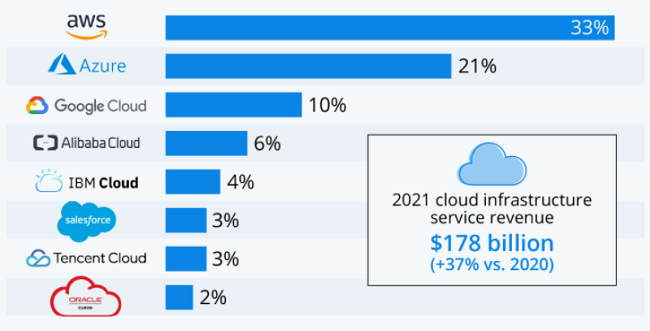
Global cloud market share of leading cloud service providers in 2022 - Statista
8. GAIA-X: A Federated Data Infrastructure for Europe - Updated
‘GAIA-X: the EU’s most important digital aspiration in a generation.’
‘With GAIA-X, Europe is building the launch pad for the “Airbus of Artificial Intelligence.”’
8.1. What is GAIA-X?
GAIA-X (European Association for Data and Cloud) is a strategic project with the aim to develop common requirements for a secure, federated, trustworthy, integrated and open European data infrastructure system that meets the highest standards of digital sovereignty while promoting innovation.
The project’s principles are openness and transparency, authenticity and trust, European digital sovereignty, modularity and interoperability.
8.2. Why do we need GAIA-X? - Updated
Europe has recognised that it can only maintain its position in the global cloud services market by uniting its resources and maintaining or even increasing its market share.
This ecosystem should facilitate both the digital sovereignty of cloud services users and the scalability of European cloud providers: the resulting federated form of data infrastructure strengthens the ability to access and share data securely and privately.
And fears are not unfounded: the figure below shows that even though the European cloud market has grown since 2017 more than threefold to more than € 7 billion in the second quarter of 2021, its market share has declined from 28% to 16%.
The ‘cloud giants’ (Amazon, Microsoft and Google) own two thirds (66%) of the regional market for infrastructure (IaaS) and platform as a service (PaaS), as well as hosted private cloud, per Synergy figures.
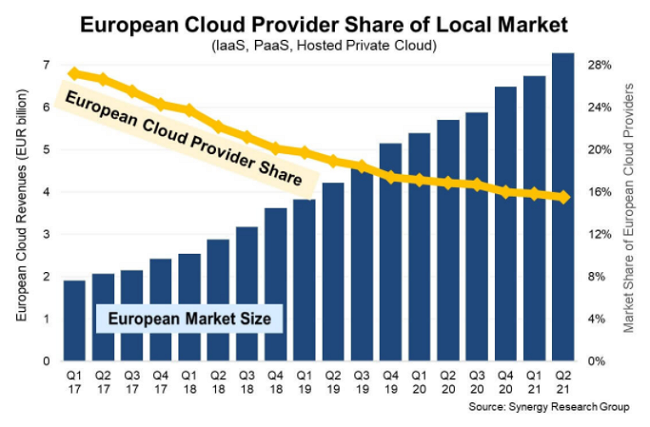
European cloud providers triple in size but still lose market – T_HQ Tech and Business
This situation raises fears in European countries: what happens when European companies’ data are stored in datacenters of non-European companies? The situation is eerily similar to when individuals or companies choose a hosting provider and can only trust that their data is secure and accessible at any time…
But what if most European companies only become tenants of one of the US datacenters and how secure their data will be, how much they will be able to access their data, and how data regulations will prevail?
An open digital ecosystem is inevitable to enable European companies and business models to compete globally. Perhaps the somewhat ambitious quotes at the beginning of the chapter should be changed to something like ‘GAIA is the last hope for Europe to retain control over its data.’ Well, it is a much more prosaic term, but it might be more realistic.
8.3. GAIA-X is open for further participation
More than 300 organisations from seven countries are already involved in GAIA-X.
But after the facts mentioned above, it is no wonder that Europe is making an effort to promote the project and win as many partners as possible to join. Furthermore, the project is open not only for European companies but also for market participants outside Europe who share the initiative’s data sovereignty and data availability goals.
GAIA-X is based on common standards which ensure transparency and interoperability. It aligns network and interconnection providers, Cloud Solution Providers (CSP), High Performance Computing (HPC), as well as sector-specific clouds and edge systems.
8.4. Benefits of GAIA-X
Beyond the strong argument mentioned above (for Europe to regain control of its data), participants of the GAIA-X project can also access AI applications and data pools via the trustworthy data infrastructure. Based on standardisation, data can be exchanged between the companies, linked with other data, processed, and evaluated. Data sharing opportunities can promote innovations, facilitate synergies, and enable new business models to be developed and scaled up.
8.5. A use case of GAIA-X
The GAIA-X Digital Space Alliance for Space: The Space Industry, just like the space-generated data, has grown significantly over the last two decades. Four European companies (OUTSCALE, CS GROUP, EBRC and RHEA Group) joined their forces and announced a new cross-border alliance to accelerate the development of ‘Space’ data value creation.
9. Detect and React: You are not alone!
‘Cloud computing is empowering; companies leveraging cloud will be able to innovate cheaper and faster.’ - Jamal Mazhar, Founder and CEO, Kaavo
This chapter briefly lists and presents the companies that are part of the Luxembourg Ecosystem and provide cloud-based solutions. The list below is not exhaustive and is not a ranking of importance.
9.1. Telindus
Telindus is one of the leaders in ICT and telecom services in Luxembourg. Its areas of expertise include fixed and mobile telecommunications, ICT infrastructure, multi-cloud, Fintech solutions, cybersecurity and managed services. Its multi-tier datacenters can be found in Bettembourg and Bissen.
9.2. Sogeti
Sogeti is a leading provider of technology and software testing. It can help you integrate cloud and non-cloud systems by performing infrastructure and application maturity assessments to move to cloud solutions.
Sogeti Cloud Ecosystem offers six cloud services: Cloud for Social, Cloud for Mobile, Cloud for BI & Analytics, Cloud for IoT, Cloud Testing Platform, Cloud Security, Cloud with IBM (SoftLayer, IBM PureFlex), Cloud with Microsoft (Azure, Testing PaaS, Cloud OS). Sogeti leverages its IBM and Microsoft Alliances and its partners’ ecosystem (HP, ServiceNow, CA, Google…) to support clients in their cloud transformation.
9.3. Post
POST offers PostCloud for Business in a Pay-as-you-use billing model and provides High resource availability flexible and scalable solutions in its Luxembourg-based datacenters. You may choose among three service models as follows: Platform-as-a-Service (CloudCorp, CloudBizz, CloudServer), Desktop-as-a-Service (CloudVDI, CloudDesk, CloudShare), and Software-as-a-Service (BusinessMail, BusinessCommunication, BusinessCollaboration). POST Luxembourg implemented an ambitious cybersecurity strategy and brought together all of its cybersecurity skills around the Department called POST Cyberforce.
9.4. Telkea
Telkea is founded in 1929 under the name of Société Luxembourgeoise de Téléphonie. It is one of the leading IT and telecom services integrators in Luxembourg. Telkea Telecom (formerly Netline) is leading the Telkea Group in the Grand Duchy. Telkea ICT is a historic player in Enterprise Networks, Unified Communications and Physical Security. Most of the services offered by ICT Telkea are also available in the cloud, allowing you to outsource everything or manage your environment in a hybrid cloud with gradual migrations.
9.5. Onepoint
Onepoint is the architect of large transformation programs for corporations and public administrations, guiding its clients from the definition of the strategic vision to its technological implementation. Their expertise enables them to provide end-to-end consulting services in relation to the transition to a cloud environment (cloudification) - among other things.
9.6. EASI
EASI (Enterprise Applications and Services Integration Luxembourg) can set up complex IT environments in Cloud2be (a tailor-made, private & hybrid managed cloud solution), combining different types of technologies including Windows-, Linux- and IBM Power (AS/400 - AIX) components.
9.7. GestComPro Europe
GestComPro is a cloud solution provider (CSP) in Luxembourg which offers personalised IT solutions for professionals (B2B): website design or e-commerce, application development, web hosting, secure cloud services, secure online backup solutions, support and advice for the digitalisation of companies (digital transition). Their product, NetExplorer, is a professional and secure solution for file sharing, online storage, and collaborative work.
9.8. Global IT Services PSF
Global IT Services PSF (GITS PSF) is an independent Luxembourg-based service provider regulated by the Commission de Surveillance du Secteur Financier (CSSF). They have been managing complex, dedicated IT and multi-cloud environments since 2005.
GITS offers high-end managed dedicated hosting, cloud services, data protection, business continuity, compliance and security solutions alongside high-performance networking and datacenter services.
Security and compliance are an integral part of their everyday work. Their business continuity and security portfolio include solutions to prevent intrusions, data leakage or data loss on all levels of the IT infrastructure.
9.9. Tuomi
Tuomi is a well-established IT company focused on programming, mobile solutions and cloud services. It is located in Trier, Germany and in Mertert, Luxembourg. Since 1995, they have been developed from IT service provider to specialists in cloud computing and experts for the conception and realisation of applications based on Near Field Communication (NFC). Their partners throughout Europe have been relying on Tuomi cloud solutions since 1998.
9.10. NSI
NSI was established in 2000 with offices in Belgium and Luxembourg. Having exclusive alliances with many well-known hardware and software vendors to provide the best integrated IT solutions to the business community, they offer cloud integrations on several platforms. NSI advises you in choosing the most suitable cloud solution, helps in the migration and deployment as well as in the cloud orchestration of your new cloud environment.
9.11. LuxConnect
LuxConnect is a multi-tier and multi-tenant datacenter facility and dark fiber provider. A wide range of value-added services, including remote hands and eyes, managed services, hosting and cloud solutions, custom-designed security solutions, etc., are operated through a network of reliable, independent partners. LuxConnect provides a fully redundant and fault-tolerant Uptime certified Tier IV infrastructure with two geographically distant and fully interconnected sites with their Dark Fiber.
9.12. Elgon
Elgon supports the digital transformation of companies focusing on workplace productivity, managed services, GDPR and hosting. Elgon is a Microsoft certified partner that shifted from a System Integrator company towards a Managed Services Cloud Provider. It adopted the Microsoft Cloud Adoption Framework and used two essential pillars of its services to offer cloud governance and cloud security solutions.
9.13. Trasys
Trasys International offers not only IT solutions, services, and consulting to help to achieve compliance with international policies and regulations but also private cloud services from its datacenters. Besides the IaaS and PaaS private cloud solutions, Trasys also offers hybrid cloud solutions.
9.14. Rcube
Rcube offers Dynamic Cloud and associated services (PaaS, IaaS, SaaS) as well as endpoint protection and E-mail Security Cloud, among other solutions.
9.15. OnePrivacy
Designed by OnePrivacy, a start-up from Luxembourg, Keexle solves many problems facing any modern company that handles sensitive data. Keexle is a fully end-to-end encrypted communication and collaboration tool where each interaction is entirely private and secure: file share, chat, cloud store, and video conference.
9.16. Calligo
Calligo supports businesses in optimising their data and their constant adherence to relevant international or industry-specific data protection legislation. We are data optimisation and privacy specialists. Calligo supports its clients across their entire range of managed data services, including IT managed services, data privacy and cloud infrastructure services.
In addition to the ones mentioned above, several other companies also provide cloud-related services. Such companies are C2D, Data Essential SA, Dimension Data Luxembourg PSF, E-KENZ SA, European Business Reliance Center (EBRC), eProseed, Omnis Cloud, EY, and System Solutions Luxembourg SA, just to name some.
10. ENISA can help!
The European Union Agency for Cybersecurity (ENISA) is the Union’s agency dedicated to achieving a high common level of cybersecurity across Europe. In this chapter, we look at what ENISA can do, how it can help, and what kinds of projects they have in relation to cloud security.
- Organisations need an IT infrastructure that can be scaled up rapidly to meet their increased demand. In the business of the digital age, this demand has made the need for large-scale datacenters indispensable. In Luxembourg, the supercomputer called Meluxina is a critical element of the data-driven innovation strategy of the Ministry of the Economy.
- GAIA-X
- Cloud Computing Risk Assessment
ENISA has conducted a risk assessment on the cloud computing business model and technologies and issued a report on its findings. This report is an in-depth independent analysis and guidance on the information security benefits and key security risks of cloud computing.
This publication contains a set of assurance criteria for governing the information security risks when going to a cloud: these criteria are designed to assess the risk of adopting cloud services, compare different cloud types, and give good advice on decision making.
As more and more companies outsource their services to the cloud, the work of companies ’IT executives has also been re-evaluated: they need to pay more and more attention to the contracts and SLAs of their cloud providers. ENISA is examining how these service contracts can be designed and monitored to optimize information security.
This report provides an insight into the prevalence of the transition to cloud services in the public sector in different EU countries. It also assists the Member States in elaborating a national Cloud strategy implementation.
This report shows how cloud providers, customers in critical sectors, and government authorities can set up cloud security incident reporting schemes in the European Union.
- Certification in the EU Cloud strategy
The goal of the European Cloud Strategy is to stimulate the adoption of cloud computing in Europe. Under this strategy, ENISA was asked to collect the results of the Cloud Select Industry Group (CERT-SIG) and propose further steps. This report shows ENISA’s findings.
- Cloud Security and Resilience Expert Group
Experts on cloud security work and meet in an informal expert group called the ENISA Cloud Security and Resilience Expert Group. This group has already produced numerous reports and studies on critical cloud computing, good cloud deployment practices, cloud computing risks, etc.
11. Conclusions
With AWS, a new server can be up and running in three minutes (it used to take Eli Lilly seven and a half weeks to deploy a server internally) and a 64-node Linux cluster can be online in five minutes (compared with three months internally) … The deployment time is really what impressed us. - Dave Powers, Associate Information Consultant at Eli Lilly and Company
11.1 Does every path lead to the cloud?
Nowadays, the IT environment and networks have become accessible to everyone, from individuals to small- and medium enterprises. Cloud-based services are one of the most dynamically developing areas of information technology. According to Cisco’s study, 94% of the worldwide workloads will be controlled by the world’s leading cloud datacentres.
Cloud computing offers plenty of opportunities to optimise core business processes and dramatically improve speed and efficiency. One prominent example of this is data collection, processing, and analysis. The transition to cloud computing can help companies keep pace with technological growth and innovation.
The cloud facilitates innovation because there is no need for massive, costly exchanges of software and IT assets. Cloud computing is infinitely agile and easier to adapt than traditional IT systems. Companies can make regular updates and adjustments without investing much time and money.
In addition to the benefits for companies, the cloud provides opportunities for an average user that the IT environment of a well-organized large enterprise would provide to its employees. Thanks to the usage-based payment method, everyone uses as much storage space (and for as long as they need) and only pays for it as much as they actually use from public cloud services.
Cloud providers’ platforms have always been the engines of automation. The complexity of these systems is constantly increasing, along with the amount of data and applications they handle, significantly reducing costs for individual companies.
Managing automated services and their performance will continue to be key for customers in choosing the platforms they use in 2022, as there are already companies today that provide hundreds or even thousands of services to their customers on one such platform.
Predicting the future is very difficult and ungrateful. If only because cloud computing is still at the very beginning of its development, its formation.
One thing is certain: the use of cloud-based services has become unavoidable nowadays, and much of our lives today are in the cloud. Be it any online services, self-driving cars, smart cities, there is some kind of cloud service behind them this way or the other.
Further diffusion and development of cloud-based technology are inevitable. Instead, the question is whether cloud security solutions will be able to keep up with this pace of development and provide adequate security for our data in the future…
Revisions
- Original document: 01/02/2021
- First revision: 01/04/2022, Chapters 3, 5, 6, 7 and 8 were updated