- 01 Jun, 2021
- Topic of the Month
1. The challenges in cybersecurity nowadays
During the COVID-19 epidemic, IT managers became key figures in businesses, and the decisions made by them greatly influenced the survival of companies. But they cannot relax even after the pandemic has subsided because they also have a crucial responsibility in restoring normalcy. Recovery, however, cannot be a simple return to previous states: the company’s entire operation must be rethought everywhere.
Businesses need teams and staff who can work autonomously and make quick decisions even in uncertain circumstances. COVID-19 caused the mass relocation of workers from the safety of their corporate network to their bedrooms, kitchen tables or studies. Because of that, the attack surface of organisations increased exponentially. This challenge has caused security to become the top technology investment priority, and cybersecurity has become the most in-demand skill set.
In 2021, IT executives who cannot find techniques to deal with intensifying cyberattacks, environmental insecurities and new situations will expose their company to a severe loss of trust. IT managers who want to avoid this are doing the right thing by carefully rethinking every aspect of their risk management strategy and doing the necessary redesign.
In the coming period, IT will play a key role in restoring normal business operations, risk management and cost optimisation. The responsibilities of IT managers are shifting slowly: they no longer only have to understand their profession, but they should become entrepreneurs, imaginers and implementers in one person who can create, sell and realise their vision.
Nowadays, threats come from many places and are often unpredictable. Reducing health, economic, social and environmental risks is now a top business requirement. Instead of focusing solely on restoring corporate operations, an effective IT leader strengthens corporate resilience by building a robust intellectual and digital infrastructure.
Consumer habits are also changing dramatically: the epidemic has completely changed people’s lives and the way businesses operate. IT organisations need to help their company with a deep knowledge of consumer intentions, expectations and reactions. This requires data analysis based on artificial intelligence, machine learning and other advanced technologies.
Market changes require more rapid innovation than ever before, and IT managers have an essential role in this area. They need to manage hybrid and multi-cloud infrastructures, services and processes without being overly tied to a particular provider.
The epidemic has forced IT managers into a changed role, and this trend not only continues but is complemented by the need for businesses to protect the health, safety and well-being of their employees while also adapting to a rapidly changing legal environment. This places an additional responsibility on IT managers, who must ensure that measures are taken to ensure the lawfulness of data management in cooperation with the HR and Legal departments.
2. The answers to the challenges
It is challenging to adapt to the changes outlined above. While IT professionals need to see the changes and adapt to them, necessary steps need to be fundamentally rethought to provide a well-thought-out, structured response to the cybersecurity challenges of the age in the long run.
These challenges can be adequately addressed in the ways described below. Awareness-raising should start with children (training courses like Virtual Digirallye, Superheroes in Action Against Cyberstalking provided by BEE SECURE – for instance) and must continue in all age groups.
The form of training can be formal, school-based, or even managed by training centres. The acquired knowledge must be continuously further developed (ongoing training, up-skilling), and space must also be given to those who come from other professions (re-skilling) so that the different way of thinking they bring can be used in the development and implementation of responses to cybersecurity threats.
Complex and rapidly changing challenges require complex and flexible response solutions that are easy to implement, widely disseminated, and can be further developed as needed.
In the following, we give some examples of possible solutions to these challenges without being exhaustive.
2.1. Formal education
University of Luxembourg
The university provides IT-related courses on master (Master in Information System Security Management) and bachelor level (Bachelor in Applied Information Technology).
BTS - Brevet Technique Supérieur
BTS offers a diploma in different IT fields, like BTS Cloud Computing, BTS Informatique, BTS Internet of Things.
There is a huge need for young talent in cybersecurity, and the enrolment for the school year 2021-22 is coming soon at Guillaume Kroll High School. Cybersecurity education is not just about developing IT skills; it is also about soft skills, project management, governance and security management.
BEE SECURE
BEE SECURE offers awareness training sessions to develop a safe and responsible use of the internet. It promotes its solutions among the general public (not only among children but also for parents, teachers and even seniors).

The formal education training sessions are compulsory for the 7-grade students. Primary and secondary school classes can book a BEE SECURE training on a voluntary basis.
2.2. Training, re-skilling and up-skilling
The growth of the digital market and the accelerated and increased cybersecurity challenges go hand in hand with a substantial increase in the demand for educators
Maybe it is not so much in the public consciousness, or the picture of it is different from reality, but still, few people choose cybersecurity as their career path. Interestingly, even a few choose this profession when they are already thinking of retraining or changing their careers as adults. At the same time, this career path is very diverse and rewarding and is open to people from diverse backgrounds from all walks of life.
2.3. Initial and Ongoing Training
The National Institute of Public Administration
The National Institute of Public Administration (INAP - L’Institut National d’Administration Publique) is a partner of the state and the municipalities of the Grand Duchy of Luxembourg in terms of primary and further training. The online training catalog offers numerous training programs in different sectors.
From the standard ECDL training, through IT security courses on cyberattacks and information leaks, and the training in reporting cyberattacks to the government CERT are all part of the training palette.
2.4. Re-skilling and up-skilling
CyberWayFinder is not only a workforce development program. Rosanna Kurrer, Co-Founder and Managing Director of CWF, wanted to bring more gender equality and diversity to cybersecurity when she launched this initiative.
Cybersecurity is traditionally a male-dominated field, and CWF set the goal to help women access a career in cybersecurity, regardless of their professional or academic backgrounds.
During the retraining, one of the most essential tasks of the CWF is to make participants in the program aware of how they can capitalise on their knowledge gained in other areas in the field of cybersecurity. Many people think that whoever works in this field writes codes, but the situation is much more nuanced and complex than that.
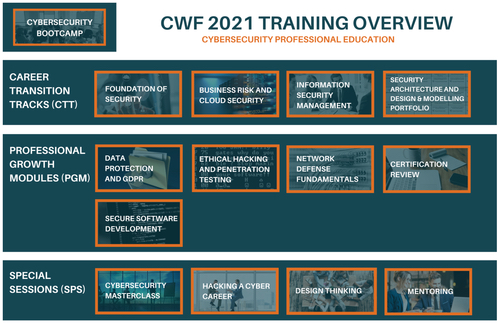
The CyberWayFinder (CWF) Training Overview for 2021 shows the opportunities available to those who want to retrain (Career Transition Tracks) or deepen their knowledge (Professional Growth Modules), or take part in some special training (Special Sessions).
The House of Training was launched in 2015 by the Chamber of Commerce and the Association of Banks and Bankers Luxembourg (ABBL), with the main mission to offer continuing professional training to meet the needs of the Luxembourg economy. It provides individual training sessions as well as certification courses.

The areas of training are very versatile; it contains 1147 training modules structured around 20 areas. The House of Training training catalog for 2021 shows the domains and the training opportunities for this year.
Some of the training courses are offered in partnership with SECURITYMADEIN.LU.
- Personal Data and Information Security - Legal Stakes and New EU Rules
- Cybersecurity – Raising employee awareness
- Ethical Hacking – Fundamentals
Lëtz Cybersecurity Challenge
Besides many other things, C3 organises the Luxembourg Cybersecurity Challenge. This annually held competition aims to find talents and encourage young people to pursue a career in cybersecurity and related disciplines.

It is a two-day event with 20 unique challenges. Participants should solve security-related tasks from domains such as web security, network security, wireless and IoT security, cryptography, exploitation, reverse engineering, forensics, puzzles, trivia and much more.
3. Shortage in cybersecurity skills
As countries digitise their economy, they increase their exposure to information technologies related incidents. These incidents can be non-intentional or driven by malicious activity. In both cases, they make more apparent the lack of relevant capability inside the targeted organisations. That is referred to as a shortage in cybersecurity skills by specialised governmental agencies and subject matter experts.
This shortage does not seem to have been really addressed through the years and is still perceived as being as sharp as it was a decade ago. Only in the most advanced economies, some reports evaluate this lack of available specialists at around 3 million people at the end of 2020, and despite the economic downturn caused by the COVID19 pandemics. If it is a logical consequence of the ever-accelerating digitisation, several issues are perceived as significant.
3.1. Different frameworks
First of all, there is no consistency in how the problem is described. Over the years, countries and organisations have designed different frameworks for managing cybersecurity skills, which led to very different perspectives, preventing any meaningful comparison between their situation, the diagnostic they make, and the possible effectiveness of the measures they have implemented to tackle the shortage.
As an illustration, one can simply look at the very different approaches from the US, the UK and France, with the first having developed a skills management toolbox around what they call the “NICE framework”, the second being more focused on the body of knowledge required to perform cybersecurity activities, known as the NCSC “CyBOK”, and the third focusing on a roles-based framework through the ANSSI “Panorama des métiers de la cybersécurité”.
On its side, ENISA, the European Agency, released in December 2019 a report on “Cybersecurity skills development in the EU”, which tries to identify more in details the reasons for the shortage. It is particularly interesting in the sense that it does not take the skills’ shortage as only a supply issue. It highlights, in particular, the problem raised by the fact that employers are, for a significant part, not keen on investing in what is described as “cybersecurity human capital”, but also may have too demanding, if not unrealistic, expectations for hires, including for entry-level jobs.
3.2. Different plans to cover the lack of skilled workers
The second issue is on how to cover for the lack of skilled employees available on the market. Most of the national frameworks are focusing on increasing the number of academic degrees providing cybersecurity qualifications.
As companies cannot wait several years before universities are able to supply them with enough graduates in cybersecurity, they are looking for other profiles who can practically address the security challenges they face. As a consequence, a significant number of security professionals are self-taught. Since they are successfully fulfilling the assigned missions, it seems extremely important also to support such profiles. One way for public authorities to do so might be by offering tools that make informal self-training easier to access.
Gamification is, in this perspective, a powerful ally, as it allows candidates who would not see them as having the abilities to enter this specialised domain through formal education. Side benefits of such informal approaches are their impact on motivation and the fact that they teach a level of resilience towards failure. This is why platforms offering both challenges and paths towards contents for self-teaching are essential to the growth of a skilled workforce in cybersecurity.
3.3. Differences in the availability of skilled labour
The third issue is the difficulty for small businesses to compete with big corporations in accessing available human resources.
If they do not have budgets for full-time IT engineering employees, it is dubious they will be in a position to hire cybersecurity specialists. They will most likely rely on third parties to support them in these matters. Practically speaking, this is often achieved through part-time consulting activities.
Many difficulties make this part-time contracting approach often impractical to implement. In particular, security involves availability when events occur and impact the information systems of the organisation. A part-time security specialist may not be readily available. However, some of the security capabilities required to slow down the degradation of a system can be embedded in software-based solutions rather than delivered through a skilful specialist. This gives some flexibility to organisations when relying on part-time support. One of the critical solutions to help organisations solve their security skills gap is to provide them with tools to find out on the existing market what is the most appropriate mix between human-based skills and machine embedded capabilities.
You may watch the below video on ‘How to bridge the gap between cybersecurity skills, education and business needs’, which was the topic of the 37th Cybersecurity Breakfast:
As per the PwC report ‘Cybersecurity coming of age’, 3.5 million cybersecurity jobs are to be filled in 2021. There is no better proof of the need for training, retraining, upskilling and education than that the reason for the shortage is the lack of adequately skilled workers.
4. How can C3 help?
One of the aims of C3 (The Luxembourg Cybersecurity Competence Center) is to give access to competence building solutions for companies by delivering training sessions regarding cybersecurity.

Besides that, C3 supports the development of cybersecurity-related school training at BTS Cybersecurity at the Lycee des Arts et Metiers.
From the C3 perspective, the goal is not to solve the theoretical discrepancies between various national or academic frameworks. Instead, to provide tools and documentation that will help companies (in particular small and medium-sized ones) understand the challenge they face in cybersecurity competence and define a way to solve it, if possible, through resources available in the Luxembourg ecosystem.
The first challenge has been to clearly understand what organisations address when they consider they lack some security skills. Most of the time, they believe the issue is at an individual level. However, this is often missing the point, as the main question is the cybersecurity competence of the organisation itself. Thinking of competence as both an individual and collective endeavour is the way to prevent being trapped in the skills shortage argument without practically improving the organisation’s overall cybersecurity competence.
From its experience and understanding of the ecosystem, C3 acknowledged the challenge to cover for the skills shortage. C3 developed a four stages approach to help organisations, including the smallest ones, as follows:
- Help organisations understand they have a problem with their collective and individual cybersecurity competence levels or maturity.
- Provide organisations with tools that allow them to identify their practical weaknesses from the perspective of the security of their information system.
- Deliver neutral and unbiased information on the threat and risk-related context so that decision-makers are in a position to allocate resources as efficiently as possible to cover for the weaknesses identified at stage 2.
- Propose systems to define the right approach to build the missing competence. This can start with a simple decision support system to find the right provider, either for training and up-skilling employees or delivering some local or cloud-based service.
