- 01 Jul, 2022
- Topic of the Month

1. Introduction
“If I wanted to see your e-mails or your wife’s phone, all I have to do is use intercepts. I can get your e-mails, passwords, phone records, credit cards.” - Edward Snowden
The word ‘authentication’ may seem a bit abstract, mystical or mysterious, but we authenticate ourselves several times a day without even thinking or knowing about it. We authenticate ourselves when we open a door with a key, visit a library with a library card, use our passport at the border or prove our identity to a police officer if we are stopped.
In fact, we authenticate ourselves from birth, as we receive an armband at birth, which has the task of authenticating us.

Photo by Phakphoom Srinorajan on Unsplash
Since the birth of IT, it has been inseparable from data protection, the compulsion to authenticate users, and the use of passwords. Every day, we use some computer device to access a certain resource (login our e-mail, use our online banking platform, etc.).
The two pillars of cybersecurity have traditionally been to restrict access and encrypt information. Accessibility is often limited by setting usernames and passwords, but there are strong arguments that this solution no longer provides sufficient protection. This article is about authentication, the importance of password usage, the need for proper password selection, and how these relate to each other to authenticate safer.
We spend most of our lives online and use more and more different online systems, which is why there is a growing demand for different types of user authentication technologies.
Organisations need to keep up with the ever-accelerating changes and realise that passwords are not the only way to authenticate users. Authentication deserves special attention in terms of protection, as its task is to ensure that the user is indeed who they claim to be. Accordingly, they are constantly looking for solutions that differentiate the real user from others with impeccable reliability.
2. What is user authentication?
“What happens with smaller businesses is that they give in to the misconception that their site is secure because the system administrator deployed standard security products - firewalls, intrusion detection systems, or stronger authentication devices such as time-based tokens or biometric smart cards. But those things can be exploited.” — Kevin Mitnick
Authentication is the security process of identifying users that request access to a system, network, or device. It covers all human-to-computer interactions that require the user to register and log in.
When users register for an account, they must create a unique ID and key pair to access their account later. In most cases, a username and password are used together (as the ID and key). Still, there can be other types of authentication factors like knowledge factors, possession factors or inheritance factors.
Basically, the user authentication process allows users to repeat access to their accounts while blocking unauthenticated users from gaining access. And we should admit that one of our most basic IT expectations is to have access to our data at any time while the same is never possible for others.
Photo by Markus Spiske on Unsplash
3. How does user authentication work?
“For invalid user name and password combinations, the service should return a 400 HTTP status code, which means that the server received a “bad request.” The service could also use the 401 (“unauthorised”) response code, but that code specifies that authentication credentials need to be in the request header, which is not quite what is required.” — Paul Dix
In order to gain access, users must prove their identity to a system or resource. Most of the time, we must provide our ID and key to confirm our identity, but there are other methods to prove who we are.
It is important to note that authorisation and authentication are often used interchangeably, but they are not the same. During authentication, the user proves while the system verifies that the user is the one who claims to be. On the other hand, authorisation determines what users can see and do when they log in. The authentication process has different steps and tasks as follows:
- Manages the connection between the user and the IT system
- Verifies user’s identity
- As per the second step, either approves or denies the request from the user
During authentication, users put their credentials on the login form of a website. The information (ID and key pair) is sent to the authentication server, where the credentials are compared with all the user credentials stored. If a match is found, the system will authenticate the user (will let them in and grant them access to their account). If the match of the ID and the key is not found, the user is prompted to re-enter their credentials.
4. Why is user authentication important?
“Ebay was involved and gave up 150 million passwords. Target was attacked and gave up 40 million credit card numbers. Attacks like these are happening on a regular basis, both in the United States and around the world, and the costs in terms of privacy or security in our financial sector are truly extraordinary.” - Donald Trump
User authentication is a method that keeps unauthorised users from accessing sensitive information. However, if user authentication is not secure, cybercriminals can hack into the system and gain access to any information the user is authorised to access.
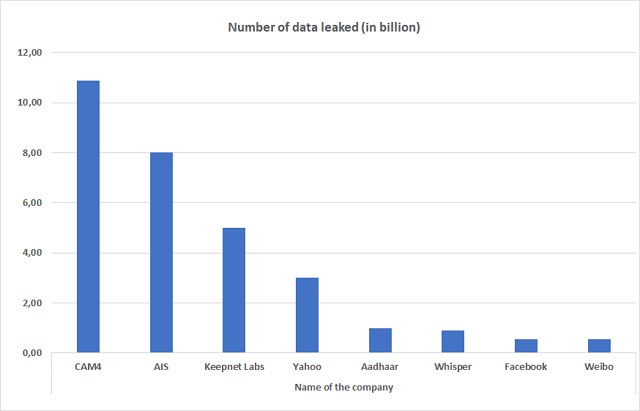
We have already witnessed several huge data breaches. There are many statistics on the Internet about the most significant data leaks over time. Below is the information on the PrivacyEnd page:
Source: Biggest Data Breaches (privacyend.com)
CAM4 is an adult cam site that experienced the biggest data breach of all time (10.88 billion records). Another very detailed analysis can be viewed on an annual breakdown of data breaches on the CompariTech website.
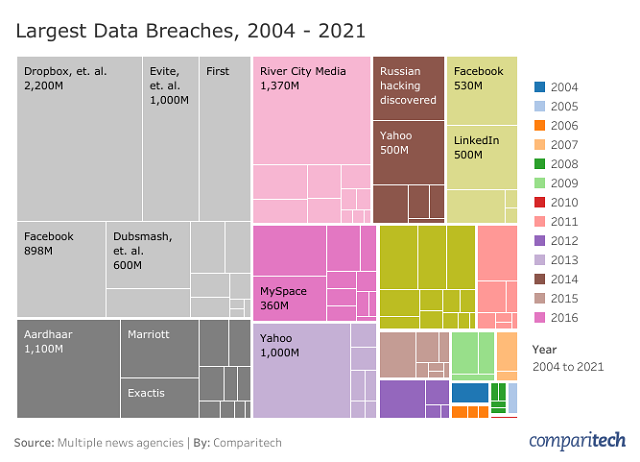
Source: The Biggest Data Breaches in History - Comparitech
In case of a data breach, cybercriminals can gain access to a system and steal information when user authentication is not secure. Without a secure authentication process, any organisation could be at risk. Cybercriminals are constantly improving their methods, and as a result, security teams face a plethora of authentication challenges.
Many sad cases have happened before us, yet companies do not seem to have learned from the bad examples. These cases were financially detrimental to the companies involved, significantly damaged their reputation, and contributed to a loss of user confidence.
It is also important to note that users can also learn from these cases: perhaps there is no longer an Internet user whose details have not been publicly disclosed or offered for sale. So, users should also think about how big ‘Internet footprint’ they want to leave behind them: how much and what type of data they want to leave on the Internet.
5. User authentication factors
“Turn on all security features like two-factor authentication. People who do that generally don’t get hacked. Don’t care? You will when you get hacked. Do the same for your e-mail and other social services, too.” — Robert Scoble
During authentication, the user must share a specific piece of information that only the user and the authentication server ‘knows.’ This piece of information is called the ‘authentication factor’, which can be categorised as follows:
5.1. Knowledge factor (authentication using something you know):
Factors the user need to know ‘by heart’ are known as knowledge factors. They can be usernames, passwords, PINs, etc. Their weakness in terms of cybersecurity is that they can somehow be linked to the user and, therefore, can be guessed. Undoubtedly, the vast advantage of this identification method is its simplicity and that the user can remember it easily since the user determines it. On the other hand, it has a lot of weaknesses as well.
5.2. Possession factors (authentication by something you own):
Anything that a user needs to possess in order to log in successfully. Physical tokens, password tokens, ID cards are considered possession factors. The security level of the authentication method depends on how easy it is to make a copy of the device in question. An ID card can be easily copied, whereas it is impossible to make a copy of a LuxTrust card.
- 4 billion people were online in 2020
- 300 billion passwords were in use in 2020
- more than 3 billion passwords were stolen in 2016
- the most used password in 2020 is still “123456”
- the biggest data breach of all-time affected 10.88 billion users (CAM4)
- an average of 95 passwords was stolen per second in 2016, and the situation has since deteriorated
5.3. Inheritance factors (authentication by something you are):
If the user’s biological characteristics are used during authentication (fingerprint, iris scan, facial recognition, etc.), it is called the ‘inheritance factor.’
5.4. Location factors
Location factors authenticate users through their location. User authentication systems can identify a user’s location by using the user’s smartphone built-in Global Positioning System (GPS) data or combining Wi-Fi and cell tower triangulation data to estimate the user’s location. Authentication systems generally do not use location factors alone to verify identity: location factor is typically used together with another authentication factor for user authentication.
5.5. Time factors
Time factors add time-based characteristics to confirm identity. Just like in the case of location factors, authentication systems generally do not use time factors alone to verify identity: time factors are typically used together with another authentication factor for user authentication. Time factors give an extra layer in user verification and authentication. Time factors are used very often with location factor to verify users. For example, if a user logs into a system from Europe and an hour later the same user tries to log in to the same system from South America, the user will not get access.
Another brilliant example of time factors usage is when a specific time span is assigned to a particular computer within which users can access the computer and its resources.
Time and location factors are often used together to try to filter out unauthorised intruders.
5.6. Authentication by something you know how to do
In this case, the authentication relies on the ability of the user to accomplish a task. The task is often to copy a distorted word (captcha field) and type it into a field. This identification factor allows people to be distinguished from computers (prove you are not a robot), but not people from each other.
5.7. Multi-factor authentication
Multi-factor authentication means the use of at least two of the above authentication factors. Within each authentication factor, we can differentiate different authentication methods. In the next part of the article, these methods will be described briefly. Further reading on authentication factors:
The more forms of authentication are used, the greater the security of access to information. Unfortunately, online services are secured at different security levels. The ideal case would be if multi-factor authentication were used everywhere. In reality, though, the cost of implementation, the constant development in security solutions and the accessibility of technology prevent it to spread widely.
Also, bringing a token or a fingerprint reader with us can be cumbersome. Therefore, the most common form of authentication remains passwords, when users share secret information with a computer that the computer can identify.

Photo by Katka Pavlickova on Unsplash
6. User authentication methods
“A lot of companies are clueless because they spend most or all of their security budget on high-tech security like firewalls and biometric authentication - which are important and needed - but then they don’t train their people.” — Kevin Mitnick
6.1. Password-based user authentication
Passwords are the most common and oldest authentication methods. Simultaneously with the birth of computing, the challenge has always been to successfully identify a particular user and thereby give them access to some IT system or resource. Passwords can be letters, numbers, special characters, or a combination of these.
The advantage of using a password is that the user creates it, but at the same time, its disadvantage is that the user has to remember it. Passwords can be stolen and misused by unauthorised people during phishing attacks. Also, there are many passwords to remember for an average person, and as a result, many people choose convenience over security.
Most people use simple passwords instead of creating trusted passwords because they are easier to remember, or if they use a more complex password, they use it to log in to multiple systems.
Passwords have many weaknesses and are usually not enough on their own to protect online information. Hackers can easily guess users’ credentials by running through all possible combinations of passwords until they find the right one.
When using a password, the user authentication process has the following steps:
- You are asked to enter your username and password
- Your credentials are sent to the authentication server and compared with the information stored on the server
- If the match is found, you are granted access, and you can log in and use the system’s resources

Photo by Yura Fresh on Unsplash
6.2. One-factor authentication
Passwords are like classic ‘ID cards’ in information systems: they are reusable in a sense that the users remember and reproduce them each time they authenticate. You may also use temporary or one-time passwords, which must be downloaded for each login attempt. This way, you may eliminate most of the shortcomings of permanent passwords: a temporary password does not require complexity or storage. However, the users usually need some kind of tool that allows them to receive passwords. The authentication system is complicated because storing a permanent password in the database is much easier than creating a new one every single time, matching accounts, and tracking expiration dates, etc.
One-factor authentication’s most significant disadvantage and danger are that it does not guarantee the authenticity of people who want to enter the computer system. It is enough to know or possess the password itself to enter the system. If anyone else learns our password, they will have the same rights to log in on our behalf as if we had done it ourselves. Of course, this type of authentication method is now very outdated since it carries many risks.
6.3. Certificate-based authentication
Certificate-based authentication technologies identify users, machines or devices by using digital certificates. The certificate contains the digital identity of a user, including a public key and the digital signature of a certification authority. Digital certificates are issued only by a certification authority and prove the ownership of a public key. This electronic certificate confirms that a public encryption key belongs to a particular user.
Users provide their digital certificates when they login to a server. The server verifies the authenticity of the digital signature and the certification authority. Then it uses cryptography to confirm that the user has associated the correct private key with the certificate.
An electronic digital signature (EDS) is also a means of authentication since it proves that the document signed by it originates from a particular person. Unfortunately, the responsibility for storing the private key rests with the owner, and as a result, there is a risk of data theft. If attackers take possession of the private key, nothing can prevent them from acting as legitimate owners.
Cryptographic methods are, of course, more reliable than passwords, but even with these methods, we cannot be absolutely sure that the user and owner of the key is the same person.
6.4. Token-based authentication
A hardware token is a physical device that is specifically designed for authentication. Token-based authentication technologies allow users to provide their credentials after receiving a unique, encrypted random string in return.
Some tokens generate one-time passwords for manual entry. In this case, the token itself is not a certificate, as the authenticity of the user is not determined by it but by a password. Tokens and smart cards are also used to store and create electronic digital signature data.
No matter how the hardware token works, the user holding the device will be real to the system. The presence of a token is in no way related to a particular person: the device can be stolen and maliciously used.
6.5. Biometric authentication
Biometric authentication is a security process that relies on the unique biological characteristics of an individual. It is an exciting area of user identification that is undergoing revolutionary development and change. There are different versions of biometric authentication (and more are likely to appear in the future).

Photo by George Prentzas on Unsplash
- Fingerprint scanners
These scanners match the unique patterns on an individual’s fingerprints. They are currently the most popular biometric technology for everyday consumers.
- Face recognition
While using face recognition, different features of a user’s face are compared to approved faces in the database: in the event of a match (in a similar way to passwords), the authentication is successful, and the user is granted access to the system or resource.
- Speaker recognition
Speaker recognition or sound biometrics examines the speaker’s speech samples and compares them to the sound samples stored in the database.
Voice biometrics allows fast, hassle-free and highly secure access to many resources. These resources can be different applications (typing without logging in), but voice biometrics can also give you access to specific rooms in an office – for example.
Nowadays, it is also conceivable to use our voice to control the elevator by saying the number of floors you want. Of course, such advanced technology cannot always be perfect:
Source: Scottish Voice Recognition Elevator - ELEVEN! - YouTube
But putting the joke aside (when the technique does not want to work due to different accents), keep in mind that sometimes our own voice can change: in the event of a cold, heavy cigarette smoking, recent tooth extraction, etc., the system may experience a significant discrepancy between the stored sample of our voice and the current sound sample and does not grant access for us.
- Eye scanners
Eye scanners use techniques such as iris recognition and retinal scanners. Iris scanners project strong light onto the eye and look for unique patterns in the coloured ring around the eye’s pupil. The samples are then compared with the approved information stored in the database. Eye-based authentication can suffer from inaccuracies if someone wears glasses or contact lenses.
The means of verifying biometric data are not solely based on human body parameters but also on behavioural characteristics. In theory, any behaviour pattern can be used for personal identification if it can discriminate against people at the individual level. For example, everyone has a unique walking pattern that can be used in gait recognition technology. The video below briefly illustrates how this technology can be used with surveillance tools to secure an area.
Source: Gait Recognition
There are a relatively large number of unique parameters: you can scan fingerprints, as you do with popular smartphone models, you can recognise faces or sounds.
Biometric authentication promises to help us get rid of the flaws of the ‘traditional’ methods discussed before: biometric parameters are unique and inseparable from the person, thus talking with much greater confidence in the authenticity of the user. In addition, no further objects or tools are needed to perform the inspection, so we cannot leave them, and no one can steal them from us.
This type of user authentication is also very convenient for the user: in the case of fingerprint, you only need to touch a scanner once, and the system does the rest.
The authentication process has the same steps as the password-based user authentication:
- The user touches the scanner with his/her finger
- The system compares the scanned fingerprint with the one on file
- If the scanned and the stored prints match, the system grants access to the user
A very detailed article on this topic: Fingerprint Scanning: 5 Things to Know Before Implementing.
This type of user authentication is often considered one of the most secure options for users because everyone’s biological characteristics are unique and not easy to copy. Nevertheless, the technology is not quite perfect so far, and experts cannot yet recommend relying entirely on biometric data. Our voice, face or iris can change over time or after having an accident – for example.
In addition to readers and their sensitivity level (or in other words, their error factors), two additional problems arise during biometric authentication:
- On the one hand, twins’ parameters are similar to the degree of confusion, especially when it comes to facial recognition.
- On the other hand, a person’s characteristics may suddenly change (for example, due to an injury) and then the user will lose access to the system.
6.6. Multi-factor authentication
Multi-Factor Authentication (MFA) is an authentication method that requires two or more independent ways to identify a user. The idea of multi-factor authentication (MFA) is to mutually compensate for the shortcomings of at least two different methods used.
- Choose unique and strong passwords
- Never use passwords more than once
- Do not choose words from the dictionary
- Do not pass on or send passwords
- Always change the preset passwords
- Use a secure password for your smartphone, too
- Use two-factor authentication
- Wherever possible, use a biometric identifier
- Use a password manager program
In the case of MFA, users can only gain access to their data, documents, or content if they prove their identity with multiple pieces of evidence. Usually, something that only they know (such as a password), or something that is theirs (such as some card, ID document), or something that is unique to them (such as some biometric identifier, fingerprint, retinal pattern, etc.).
Examples of multi-factor authentication include using at least one of the following with a password: Captcha tests, codes generated from the user’s smartphone, fingerprints, voice biometrics or facial recognition.
In practice, two-factor authentication (2FA) is most often used. Two-factor authentication uses a combination of two components mentioned above. For example, two-factor authentication occurs when an ATM asks for our credit card for a withdrawal and adds a PIN (which only we know).
Two-level authentication is also provided by most platforms and devices, especially when we entrust our data online. We can use it on numerous online services, and we can set it up on our personal computer, smartphone, tablet, and most operating systems.
The second level of authentication is typically related to our mobile phone. You can access the unique, secondary code via SMS, instant message or the code generation application installed on your phone, which you must enter in the login interface.
Although two-level authentication does not provide 100% protection, by setting it up, we can build an extra critical line of defence around our personal content, significantly reducing the chances of identity theft and fraud. Anyone who hacks our password will not be able to access our data because of the second layer of authentication.
However, keep in mind that authentication with two factors does not solve password protection issues: it only complicates the attacker’s task by introducing another factor.
7. Passwords
“Passwords are like underwear: you don’t let people see it, you should change it very often, and you shouldn’t share it with strangers.” - Chris Pirillo
We spend most of our lives online, posting on social media sites, shopping, working, banking, or just learning. An average user has dozens of online accounts that store a wealth of personal and financial information. Users have to remember too many, sometimes hundreds of passwords, so, unfortunately, they use almost identical to the original or easy to guess passwords.
Logging in with a username and password is also the most popular authentication method on computers, web services, and smart home devices. This authentication method is often the most important or the only security feature protecting against unauthorised access.
Since 2013, World Password Day has been held worldwide every year on the first Thursday in May. It is intended to draw attention to the importance of conscious password use.
As per the Microsoft Secure Blog, there were about 4 billion people online in 2020, and this number increases exponentially. As the number of users increases, so does the number of passwords in use (300 billion in 2020!) and, in parallel, the likelihood of cyber threats. As per TechJury, Companies experienced an average of 22 security breaches in 2020, but it took an average of 6 months for them to detect a data breach.
According to the article published by Cybersecurity Ventures and Thycotic, more than 3 billion passwords were stolen in 2016. To make this colossal number more understandable, we can also say that 8.2 million passwords a day or 95 passwords every second were stolen…
Because of the accelerating frequency and rising costs of security breaches, Cybersecurity Ventures forecasts a depressing $ 6 trillion a year damage in cybercrime.
7.1. What is a password?
A password is a set of secret characters or words used to authenticate access to and secure a digital system. For those who are visual type and prefer videos, a short video from CASES:
Source: Passwords - YouTube
7.2. What is a secure password?
“Choosing a hard-to-guess, but easy-to-remember password is important!” - Kevin Mitnick
Password security begins with creating a strong password. A strong password is characterised by:
- At least 12 characters long, but at least 14 are better.
- A combination of uppercase, lowercase, numbers, and symbols should be used.
- It does not contain words from a dictionary nor a name of a person or organisation.
- It is significantly different from your previous passwords.
- They are easy to remember but difficult for others to guess. It is a good idea to use a memorable phrase or sentence.
7.3. Password hacking
Guessing passwords or obtaining them with computer decryption tools is called password hacking. A typical method is to try frequently used passwords and personal information or try words and their combinations using electronic dictionaries and password crackers. If these do not work, the so-called brute force method remains, which tries a variety of possible characters to find the password.

Photo by Towfiqu Barbhuiya on Unsplash
The strength of a password is determined by the extent to which it can withstand password hacking attacks. More specifically, it is defined as follows:
- Length: how many characters the password contains?
- Complexity: does it use a combination of letters, numbers, and symbols?
- Unpredictability: can it be guessed easily by an attacker?
7.4. Use password strength checkers!
You may use special applications (password strength indicators, password strength checkers) online. One of them is called The Password Meter and looks as follows:
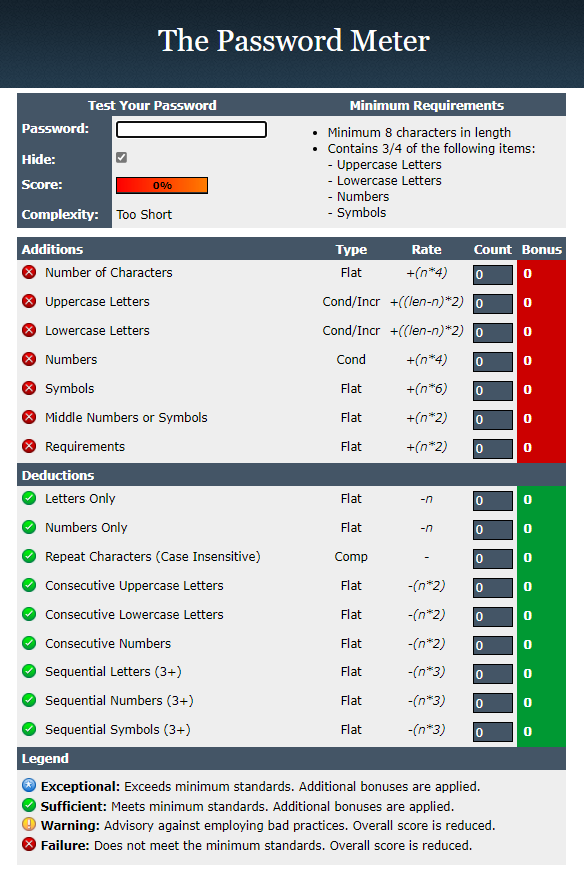
Source: Password Strength Checker (passwordmeter.com)
The biggest advantage of this checker is that it provides immediate visual feedback of the password’s strength and shows where it can be improved. By using a tool like this, you can reduce the habits that result in weak passwords and increase the strength of your passwords by knowing what factors to look out for when creating a password.
What are at risk?
- User: The security of users’ data is compromised if unauthorised people gain access to their data (for example, by hacking into their electronic mailbox).
- System operation: Obtaining and misusing administrator passwords can compromise or shut down systems. Hacking passwords can be the initial step in more damaging abuses.
- Information security: Hackers can gain large amounts of data by unauthorised passwords of key users and administrators and hide the traces of their unauthorised intrusion.
- National security: By obtaining the passwords of the information systems used in public administration and national security, it is possible to cause exponentially greater damage: to get the data of national systems or endanger the operation of infrastructure elements.
8. Tips for safer password usage
“Treat your password like your toothbrush. Don’t let anybody else use it, and get a new one every six months.” - Clifford Stoll
8.1. Choose unique and strong passwords!
Perhaps many of us agree that creating a strong and secure password is not that complicated, and everyone should do it. Still, several statistics, surveys, and privacy incidents have already shown that few people accept this advice.
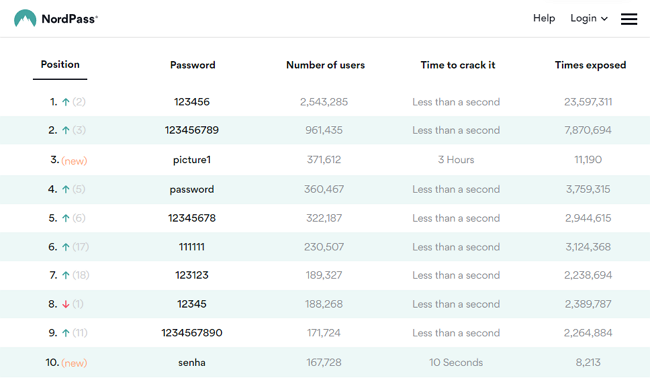
Every year, NordPass publishes a list of the most commonly used passwords, which showed that in 2020, easy-to-guess number combinations such as “123456”, “123456789”, and “12345678” continued to be the most popular among users.
The list details how many times a password has been revealed (Times exposed), how many users used them (Number of users), and how long did it take to crack (Times to crack it). NordPass also compares the worst passwords for 2019 and 2020, highlighting how their positions have changed. The green arrows indicate an increase in the situation, while the red ones indicate a fall:
Source: NordPass
Surprisingly, the password “picture1” came third on the list of imaginary worst passwords. Still, it can be seen that six of the top ten passwords contain the simplest number combination, while the “password” password has moved up to fourth place.
An attacker can often access password databases for online services, so the service provider should not store any passwords as text. Attackers can try billions of passwords per second, so it is necessary to guess strong passwords. However, such passwords are often difficult to remember, so let’s look at some procedures on how the user can remember even seemingly complicated passwords more easily. We can also easily find websites or mobile apps that generate strong passwords for us.
The first letter method:
Think of a sentence you are sure to remember and take the first letter or one of the marked letters from each word. However, be careful not to choose a sentence that someone else might come up with that could relate to you or your environment. If you think of a familiar saying, excerpt, or poem as a sentence, change its content somehow.
Hugh’s Secure but Easy to Remember Password Generator is a free online service where you can type a phrase (which should be a minimum of eight words), and the app creates multiple password variations:
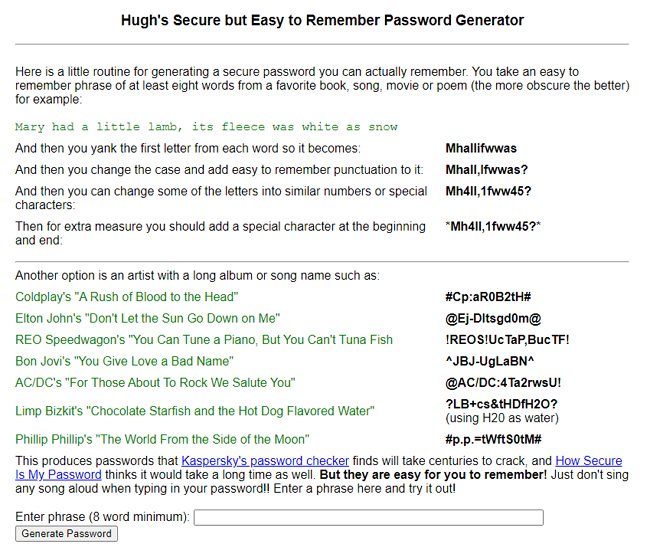
Source: Hugh’s Secure but Easy to Remember Password Generator
Whole sentence method:
If you can type quickly, a whole sentence can be used as a password. It is also possible that the sentence contains meaningless fantasy words or consists of randomly spaced words.
Generate a random password:
In some browsers, it is possible to generate a random password and save a password to a safe without you seeing it. This method is often the most convenient and secure as long as the password safe encrypts the data well and is not accessible to third parties.
8.2. Never use passwords more than once!
Use different passwords for different accounts. As we manage more and more accounts each year, it is getting more difficult to guess and remember a strong password for each of our profiles. A good solution for this is a password management program that can store a lot of complex passwords.
Attackers have collected many real passwords in recent years, with billions of passwords becoming public. Attackers, in turn, use these to illegally log on to another service or crack other similar passwords that have been minimally changed. You can check if your e-mail address is affected on the Identity Leak Checker page. A Have I Been Pwned? website is a place to see which passwords have become public. This website contains 613,584,246 leaked passwords that were previously exposed in data breaches.
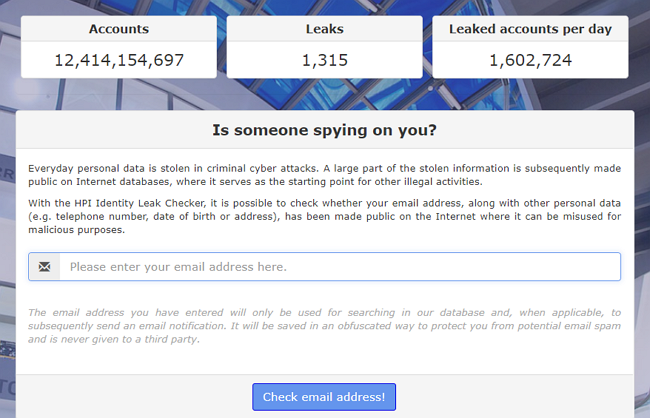
Source: Identity Leak Checker
8.3. Don’t choose words from the dictionary!
Attackers today can automatically try out many combinations in a short amount of time. Therefore, a good password is not a concept or combination of concepts found in a dictionary (‘Winter1971’), nor is it a combination or recycling of them. The only exceptions are long passwords, which consist of a series of random or unrelated words.
8.4. Do not pass on or send passwords!
Do not pass on passwords, especially do not send them in an unencrypted e-mail or save them in an unencrypted document. Many people send themselves their passwords in an e-mail attachment so they do not forget them. However, they do not think that all the passwords sent in the e-mail will be meaningless the moment someone accesses their e-mails themselves, and thus the passwords in the list are revealed.
8.5. Always change the preset passwords!
Preset passwords, such as IoT devices, are often not random for software packages but are the same on all devices. Therefore, they must be changed immediately after first use.
8.6. Choose a secure password for your smartphone too!
Even if secure passwords are harder to enter on a smartphone or tablet, you still need to enter a secure and long password there. Four-digit PINs are usually not sufficient. Because of the biometric identification methods available, people use passwords relatively infrequently. Still, care must also be taken because not all manufacturers provide a high level of security for biometric identification.
8.7. Use two-factor authentication!
More and more interfaces are making it possible to use multi-factor authentication, which provides an extra layer of security for users as they require additional authentication in addition to entering a password. The most common way is to enter the code you received in an SMS or e-mail. Still, an even more secure way is to use a dedicated authentication application or hardware solution, such as authentication tokens.
Many web service providers offer so-called two-factor authentication. When activated or used with a new device, you must enter another ID, as is common in online banking. This second factor works on a different communication channel, so knowing the password alone is not enough for a successful attack.
For example, you may be familiar with the use of tokens in banking or SMS confirmation codes on your phone to confirm your access. Although it can degrade the user experience, it provides enhanced security if an attacker needs to access two of your devices (e.g. your phone and token, or your computer and phone) at the same time to get through your security lines.
8.8. Where possible, use a biometric identifier
Nowadays, more and more mobile devices or peripherals connected to a desktop computer are capable of biometric access. Our phones’ facial recognition or fingerprint reader features have become so natural that they do not detract from the user experience yet provide a solid front line of protection for our mobile devices.
8.9. Use a password manager program
It is a digital safe where you can easily place passwords used in different places. All you have to do is memorise the master password. That way, you do not have to worry about remembering your passwords, nor do you have to worry for minutes about what code you entered earlier for your rarely used accounts.
The password manager requires only a strong password to be used and can store other login information, username-password pairs, or even other secret data in the virtual safe opened with it. Such an application could be Lastpass or 1Password.

Photo by Jason Dent on Unsplash
8.10. Stay up to date!
Keeping our passwords up to date is an annoying but not negligible constant task. We must update our passwords regularly (depending on how important data we protect, we can update them annually, semi-annually, or even monthly) and make sure we store them securely and only accessible to us.
It is advisable to regularly renew all your important passwords, especially if you share a particular device with other users. You may also want to change your code if your antivirus detects malware. At haveibeenpwned.com, you can check for your leaked and disclosed passwords. It contains more than 11 billion stolen name-password pairs.
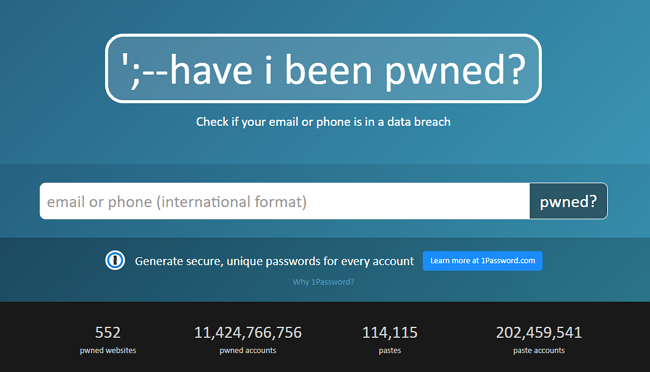
Source: Have I Been Pwned: Check if your e-mail has been compromised in a data breach
8.11. If you run out of ideas, use a password generator
From the users’ point of view, it is inconvenient that websites may have different expectations about the passwords that can be used (number of characters required, special characters needed or not, etc.). There are also websites for generating secure passwords, such as the Secure Password Generator, where you can create a password that meets the requirements of a given online service (a certain number of characters, etc.) and is secure.
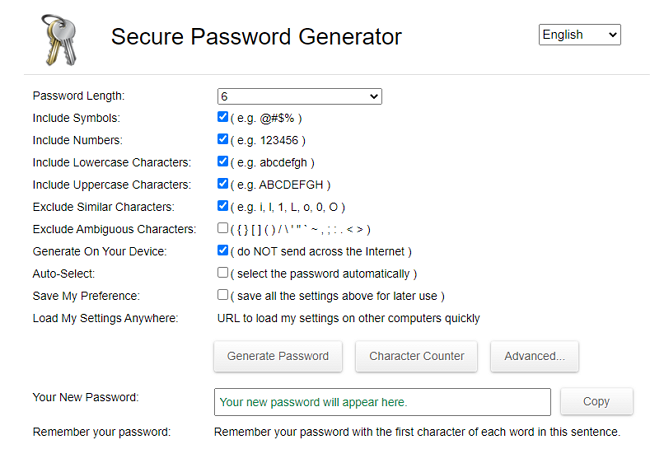
Source: Secure Password Generator
There are several online password generators to choose from. Another one is called Domain Diagnosis. But there is also a password generator specifically for kids: called Dinopass.
8.12. Don’t be fooled into entering your passwords!
Internet criminals may try to crack your password. Still, sometimes it is easier for them to exploit the weaknesses of human nature and deceptively try to deceive you into entering your password. Do not let scammers fool you once you have taken many precautions to create a strong enough password. Be careful of phishing scams and social engineering attacks.
9. Keeping passwords secure – password hygiene
“The whole notion of passwords is based on an oxymoron. The idea is to have a random string that is easy to remember. Unfortunately, if it’s easy to remember, it’s something nonrandom like ‘Susan.’ And if it’s random, like ‘r7U2*Qnp,’ then it’s not easy to remember.” - Bruce Schneier
Once you have created a strong password, follow these guidelines for security:
- Do not share your password with others. Not even with a friend or family member.
- Never send your password via e-mail, instant message, or any other untrusted communication channel.
- Use a unique password for each site. If your data is stolen from one site, attackers will use your credentials on other sites, such as banking, social networking, or online shopping.
- If you do not want to remember more passwords, you may want to use a password manager. The best password managers automatically update stored passwords, store them encrypted, and require multi-factor authentication for access.
10. Does your password matter?
“A computer that can crack an 8-character password in 4.2 hours would need 5.7 trillion years to crack a 16-character one.” – unknown
(Source: Password Cracking Is Easy: Here’s How to Do It | by Kenny L. | Medium )
After so much information, advice and analysis, this question may seem strange. The reader can rightly assume that if he has learned so much on this topic, he will no longer be in big trouble since his data is safe and unauthorised access to his data will not happen as he has done his best not to crack his passwords.
Yet we have to ask this question, and unfortunately, no matter how much it hurts, we have to face the facts. Analyses and data show that passwords’ strength and complexity alone do not mean much: sooner or later, they are deciphered anyway.
Probably you still remember that back in 2012, 117 million usernames and passwords leaked from LinkedIn. At that time, it affected 73% of all LinkedIn users.
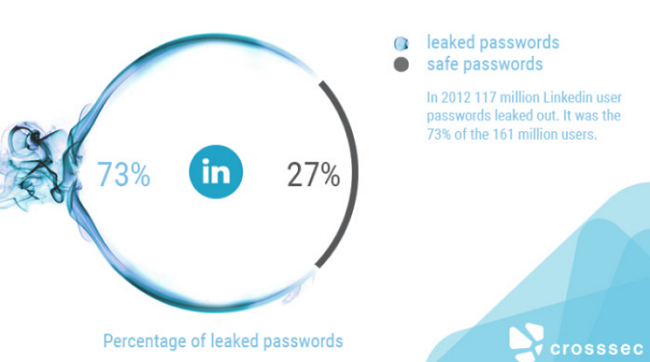
Source: 117 Million LinkedIn e-mails and passwords leaked
Alex Weinert, Group Program Manager for Identity Security and Protection at Microsoft, was one of the engineers who came up with the idea to ban passwords that became public due to password breaches. He was one of the engineers who demanded not to reuse passwords that had fallen victim to password hacking and made public.
“Never use a password that has ever been seen in a breach.” - Alex Weinert
He demanded this because one of the methods of password hackers is to use stolen password databases to try passwords that already existed somewhere and then modify them slightly until they find the password that the user is currently using.
It stems from a human weakness: we cannot remember many passwords once we have managed to memorise a password that is a bit complicated (yet it is still extremely simple for computers), we tend to use it in several places or with a bit of modification.
In 2019, Alex wrote a genuinely revealing, slightly creepy and realistic article on this topic with the title Your Pa$$word doesn’t matter. Although his stats come only from Azure Active Directory connected accounts, we can draw crucial conclusions from the data. He shows the different attack types, their frequency, how difficult it is for the hackers to carry them out, how users help attackers, and finally: do our passwords matter at all? Below, I present through a simplified table his main findings (the link to the entire document can be found below the image):
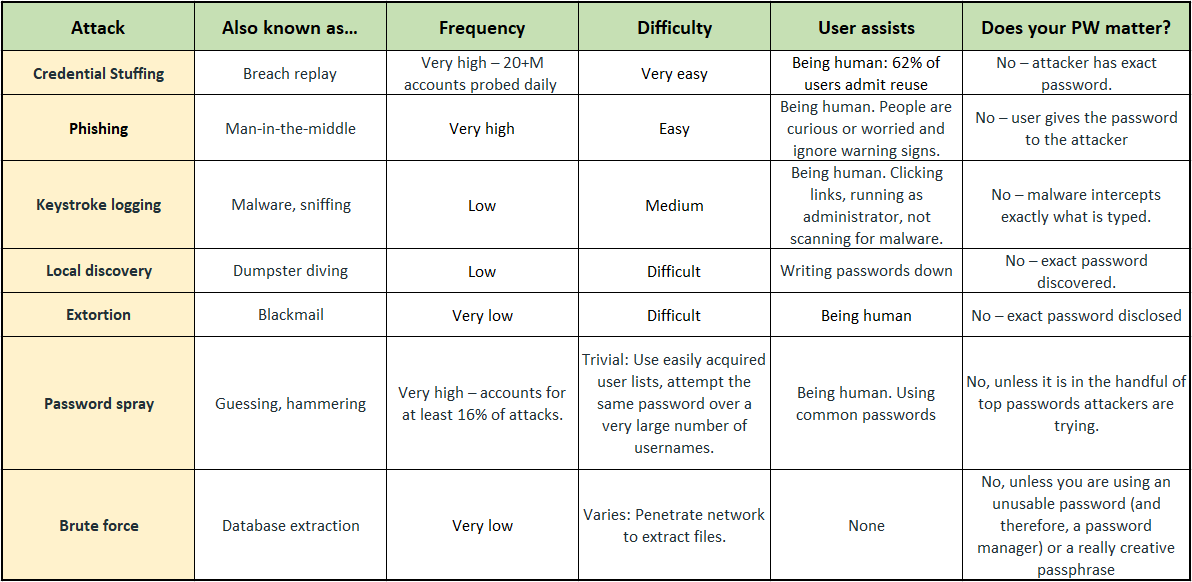
Source: Your Pa$$word doesn’t matter - Microsoft Tech Community
The data in the spreadsheet is very thought-provoking and can make us realise that using the password alone is not worth much. Passwords are (no matter how complicated they are) static: it often takes months for us to change them. Between the two changes, however, we give hackers room to decipher the code either by guesswork or by brute force.
Therefore, in addition to the mere use of passwords, we must incorporate another protection mechanism to save our data: use two-factor authentication. Beyond the password, send a password via SMS, biometric authentication or anything that is another line of defence that, in addition to the static password, is dynamically trained, temporary, and thus can radically reduce the chances of password cracking.
Tech giants like Google and Apple (among others) call for the broadest possible introduction and standard application of passwordless user authentication because passwords are the most significant gap in cybersecurity and the protection of their users’ data. Companies only store their users’ data and have little influence over how strong passwords their users create. Of course, they can prescribe at least how many characters the password should be, contain special characters, etc., but in the section above, we saw how much protection this means in itself.
11. Passwordless authentication
“I never surf (the Net). I don’t know the password.” – George Harrison
Features like multi-factor authentication can help build security for your organisation. Still, users are often frustrated that they have to remember an additional layer of protection in addition to their passwords.
Passwordless authentication methods are more convenient because you do not have to remember passwords and are compatible with most devices and systems. In addition, they are virtually unbreakable in phishing.
Passwordless authentication is a type of multi-factor authentication (MFA) that replaces passwords with a more secure authentication factor, such as a fingerprint or PIN.
Source: Why Big Tech Wants You To Ditch Your Password - YouTube
Passwordless authentication relies on a cryptographic key pair with a private and a public key. A user who creates a secure account uses a tool (like a mobile app or a browser extension) to generate a public-private key pair. The private key is stored on the user’s local device and linked to an authentication factor, such as a fingerprint, PIN. The public key is provided by the website, application, browser, or other online systems for which the user wants to create an account.
12. How can SECURITYMADEIN.LU help?
“We live not by things but by the meaning of things. It is needful to transmit the passwords from generation to generation.” - Antoine de Saint-Exupery
CASES (Cybersecurity Awareness and Security Enhancement Services) is part of SECURITYMADEIN.LU. It has multiple services available to the public to raise awareness concerning cybersecurity in general and safe password usage and hygiene in particular.
On the CASES website, you may read articles about Authentication, what to do in case of Online Identity Theft, or if your account becomes compromised. Also, you may get valuable information regarding E-banking best practices and LuxTrust card usage. The video below shows how to adopt the right reflexes when using the “Luxtrust” tools (in French):
Source: Luxtrust - YouTube
Keep in mind that the weakest link in using LuxTrust is the user. This is the reason why awareness-raising is so important. On the CASES website, you may also get advice on what to do if one of your colleagues wants to know your password.
In addition to professional CASES training sessions, you may also get valuable information on the SECURITYMADEIN.LU portal, where you can read articles, register for the Cybersecurity Breakfast series, watch the Lëtz Talk About Cyber series or read cybersecurity-related news, besides other things.
For example, you may read the article Sextortion scam e-mails: “I know your password", in which you can find more information about this type of cybercrime which is also an excellent example of how attackers can track down our passwords.
The Computer Incident Response Center Luxembourg (CIRCL) is also part of SECURITYMADEIN.LU, with the initiative to gather, review, report and respond to computer security threats and incidents. One of their services is information leak analysis, and you may check the list of reported detected information leaks in Luxembourg.
Source: CIRCL – AIL Analysis of Information Leaks
CIRCL develops different tools, one of which is called the AIL- Analysis Information Leak framework. It is open-source software that can be installed to find a leak of information.
Besides tools you may use, you can also find valuable advice on the CIRCL website about What to do when you can’t trust your communications channels or How to create strong passwords.
On the CYBERSECURITY Luxembourg website, you may find public and private entities which focus on authentication and password-related matters. Among many entities, one example can be Passbolt which is an open-source password manager provider that aims to improve the information security of small and medium organisations. Passbolt is part of the Luxembourg cybersecurity ecosystem.
TIP: we know that the majority of threats and attacks are coming with phishing e-mails. If you use SPAMBEE to handle suspicious e-mails and Passbolt as your password manager, you are making a huge step forward in securing your e-mail and protecting your data. SPAMBEE is a joint initiative of BEE SECURE, the CNPD and the Cybersecurity Competence Center Luxembourg (C3), and all four are part of the Luxembourg cybersecurity ecosystem. SPAMBEE allows you to analyse dubious e-mails to determine if they are SPAM or phishing.
13. Conclusions
“Bad password usage patterns are common to users regardless of their age, gender, or personality type.” – Joe Siegrist, Vice President and CEO of LastPass
Passwords are an archaic solution to authentication that we should have surpassed a long time ago - yet almost every system we come across uses passwords instead of more secure biometric identifiers. The problem with passwords is that they are easy to obtain and crack - provided the user does not take the proper precautions.
Of course, the biggest problem is that to use all services securely, we would have to choose a unique password everywhere - which is long and complicated enough. These should also be kept in mind and recalled immediately if necessary.
Sometimes the service providers make a mistake, and even though you create a secure password, somehow, your login details are still made public. If a problem has occurred, you can do the following:
- change your password immediately
- if you used the previous login data on several pages, replace them with another one (preferably different from each other)
- if you have not done so before and it is possible, turn on two-step authentication
You may accidentally enter your login information on a phishing page. In this case, in addition to the above, it is worth doing the following because not only fraudsters can access your data on the phishing site, but they can also introduce malicious programs, extortion programs and other digital malware into your system:
- check the machine with a reliable antivirus to see if it is infected
- if you experience infection and the antivirus can remove it, then change the passwords for the affected accounts and your system, even if you have already done so
Security companies list the weakest passwords that are most easily hacked by hackers year after year.
Most users are aware of the risks but do not change their bad habits, even though they know they provide sensitive information to potential hackers.
Technological developments in recent decades have significantly changed our daily lives. Information, communication and other services are available to everyone, but most users today are no longer IT professionals.
The technology that surrounds us, and from which we cannot disassociate ourselves, is evolving faster and faster, and it is getting harder to keep up. We store more and more things in digital form and use the Internet more and more diversely.
Make sure you store your data securely, stay up to date on recent technological advancements and remain resilient to change your behaviour and attitude if needed to secure your digital footprint.